L’Allemagne recherche des moye...
L’Allemagne recherche des moye...
Nations Scramble to Develop On-Orbit Satellite Defense Capabilities
The race is on to safeguard our satellites in space, with nations like France, Germany, India, and Japan now scrambling to develop their own on-orbit defense capabilities in a bid to match the world's top space powers. This emerging trend signals a major shift in the global space landscape, where protecting assets in…
#SpaceDefense #OnorbitProtection #SatelliteSecurity #NationState #EmergingThreats
Ukraine’s enforcement of verified-only Starlink terminals introduces a new model of satellite access control in conflict zones.
Operational implications reportedly include:
• Disruption of adversarial drone command-and-control
• Attempts at fraudulent terminal re-registration
• Social engineering targeting civilians
• Cyber exploitation of reconnection attempts
The incident demonstrates how:
– Commercial satellite services are high-value C2 infrastructure
– Identity verification becomes a strategic defense control
– Space-based connectivity is now an attack surface
From a security architecture standpoint, this is a case study in satellite access governance under active conflict conditions.
How should satellite providers balance neutrality, compliance, and operational control?
Source: https://therecord.media/starlink-restrictions-hit-russian-forces
Engage below.
Follow TechNadu for structured cybersecurity and threat intelligence reporting.
#Infosec #SatelliteSecurity #C2Infrastructure #CyberDefense #SpaceTech #ThreatIntelligence #DefenseCyber #SecurityArchitecture #HybridWarfare #TechNadu
Blue Origin’s planned TeraWave constellation highlights how satellite communications are increasingly part of enterprise and government resilience strategies.
High-capacity space networks can reduce dependence on terrestrial links, but they also expand the attack surface - across satellites, ground infrastructure, and control systems.
How should security models evolve as space becomes part of core network architecture?
Share your insights, engage in the discussion, and follow @technadu for neutral, security-focused reporting.
#SatelliteSecurity #CriticalInfrastructure #CyberResilience #SpaceSystems #InfoSec
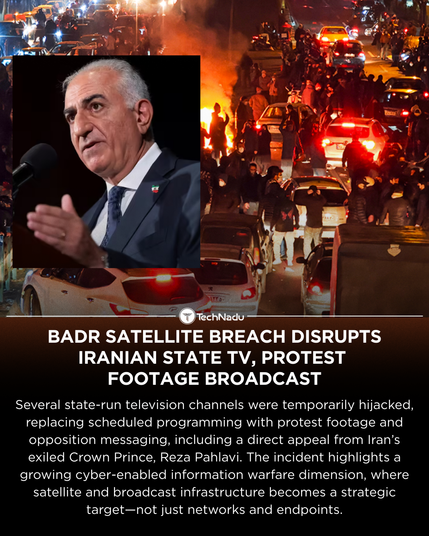
A breach of the Badr satellite disrupted Iranian state TV, airing protest footage and opposition messages nationwide.
An example of cyber tactics shifting toward broadcast and satellite infrastructure.
What does this mean for satellite security going forward?
Researchers from UC San Diego & UMD exposed a massive satellite data leak - half of all geostationary signals are unencrypted, revealing calls, texts, and even military operations.
Intercepted with just $800 in equipment.
Security researchers are increasingly exploring vulnerabilities in commercial and government satellites. From intercepting unencrypted signals to analyzing firmware flaws, these experiments reveal how critical spaceborne systems can be compromised. While controversial, this research drives the development of stronger encryption, more secure communication protocols, and resilient hardware designs. It also highlights a growing frontier in cybersecurity. One that extends beyond terrestrial networks and challenges our assumptions about where digital security will take us.
#SatelliteSecurity #CyberResearch #SpaceTech #HackingFrontiers #TechInnovation
#Cybersecurity #SpaceTech #SatelliteSecurity #SpaceDefense
https://www.ladepeche.fr/2025/07/18/guerre-en-ukraine-la-russie-veut-cibler-les-satellites-des-pays-europeens-plusieurs-perturbations-deja-recensees-12832509.php
#Space #Science #AerospaceEngineering #SatelliteSecurity #EmergingTrend
Guerre en Ukraine : la Russie veut cibler les satellites des pays européens, plusieurs perturbations déjà recensées
Selon une information rendue publique mercredi 16 juillet, la Russie a affirmé vouloir cibler les satellites commerciaux et de diffusion des pays européens qui, selon elle, aident l’armée ukrainienne.