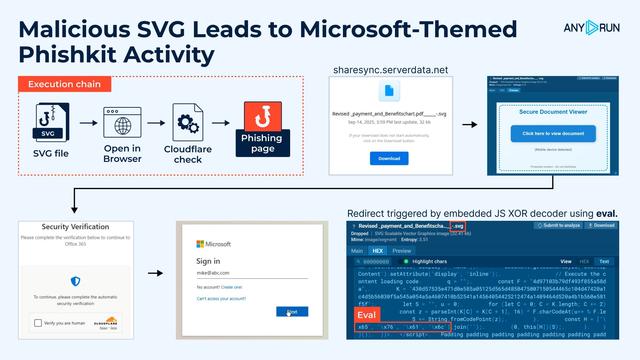
🚨 Malicious SVG Leads to Microsoft-Themed #PhishKit.
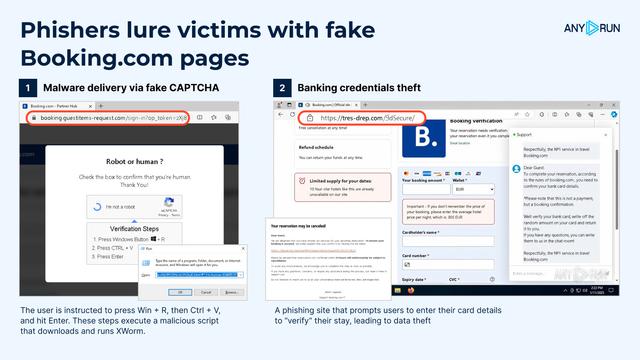
⚠️ We observed a #phishing campaign that began with testing activity on September 10 and scaled into full spam activity by September 15. A legitimate domain was abused to host a malicious SVG disguised as a PDF. Attackers hide redirects and scripts inside images to bypass controls and social-engineer users into phishing flows.
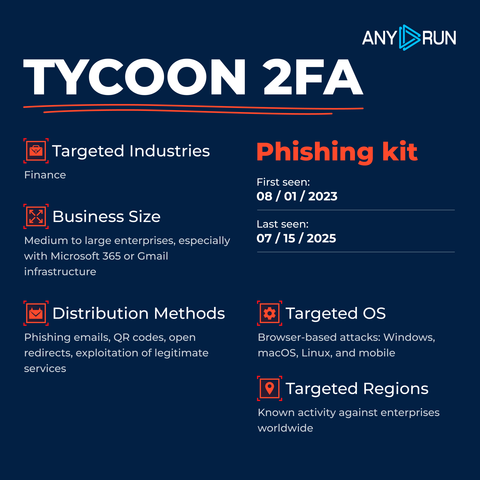
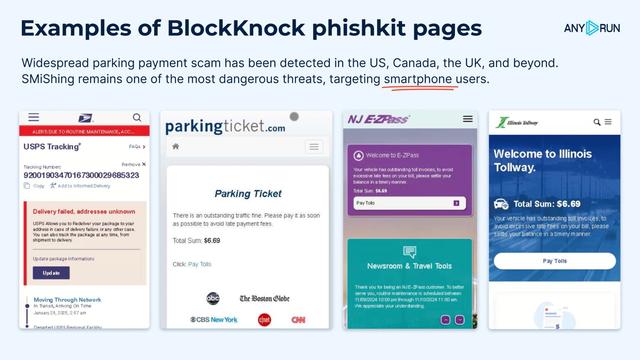
🎯 This case shows a structured infrastructure similar to a #PhaaS framework, showing how attackers rely on robust, scalable models for mass credential harvesting, now a standard across the phishing ecosystem.
For enterprises, the risks are clear: blind spots in monitoring, delayed detection and response, and an increased risk of credential theft or data breach.
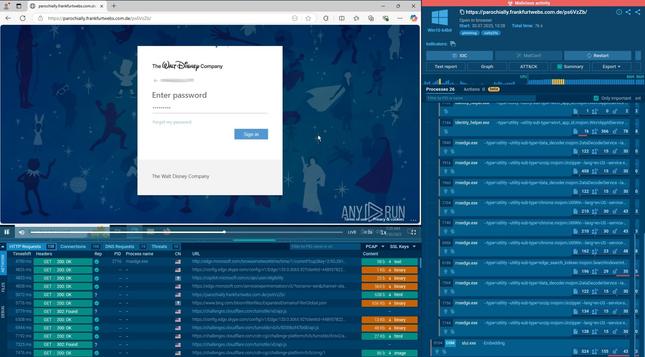
👨💻 When opened in a browser, the SVG displays a fake “protected document” message and redirects the user through several phishing domains. The chain includes Microsoft-themed lures such as:
🔹 loginmicrosft365[.]powerappsportals[.]com
🔹 loginmicr0sft0nlineofy[.]52632651246148569845521065[.]cc
❗️ The final phishing page mimics a Microsoft login and uses a #Cloudflare Turnstile widget to appear legitimate.
Unlike standard image formats, SVG is an XML-based document that can embed malicious JavaScript or hidden links. Here, the redirect was triggered by a script acting as an XOR decoder, which rebuilt and executed the redirect code via eval.
🎯 For SOC analysts, being able to trace every redirect step and uncover hidden payloads is critical to investigating phishing campaigns. See execution on a live system and collect #IOCs:
https://app.any.run/tasks/78f68113-7e05-44fc-968f-811c6a84463e?utm_source=mastodon&utm_medium=post&utm_campaign=malicious_svg&utm_content=linktoservice&utm_term=160925
For CISOs, the critical takeaway is that attackers exploit trusted platforms and brand impersonation to bypass defenses, directly threatening business resilience and user trust.
🔍 Use these TI Lookup search queries to expand visibility and enrich #IOCs with actionable threat context.
Suspicious SVG downloads:
🔹 https://intelligence.any.run/analysis/lookup?utm_source=mastodon&utm_medium=post&utm_campaign=malicious_svg&utm_content=linktoti&utm_term=160925#%7B%2522query%2522:%2522commandLine:%255C%2522Downloads%255C%255C%255C%255C*.svg%255C%2522%2522,%2522dateRange%2522:180%7D
Microsoft-themed phishing domains:
🔹 https://intelligence.any.run/analysis/lookup?utm_source=mastodon&utm_medium=post&utm_campaign=malicious_svg&utm_content=linktoti&utm_term=160925#%7B%2522query%2522:%2522domainName:%255C%2522microsoft.*.*%255C%2522%2522,%2522dateRange%2522:180%7D
🔹 https://intelligence.any.run/analysis/lookup?utm_source=mastodon&utm_medium=post&utm_campaign=malicious_svg&utm_content=linktoti&utm_term=160925#%257B%2522query%2522:%2522domainName:%255C%2522%255Eloginmicr?sft*.cc$%255C%2522%2522,%2522dateRange%2522:180%257D
IOCs:
Revised _payment_and_Benefitschart.pdf______-.svg
A7184bef39523bef32683ef7af440a5b2235e83e7fb83c6b7ee5f08286731892
Strengthen resilience and protect critical assets through proactive security with #ANYRUN 🚀