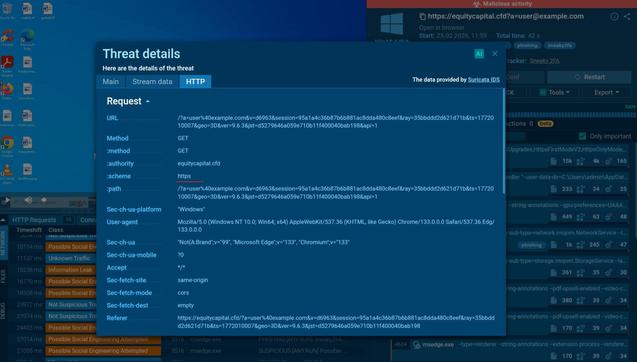
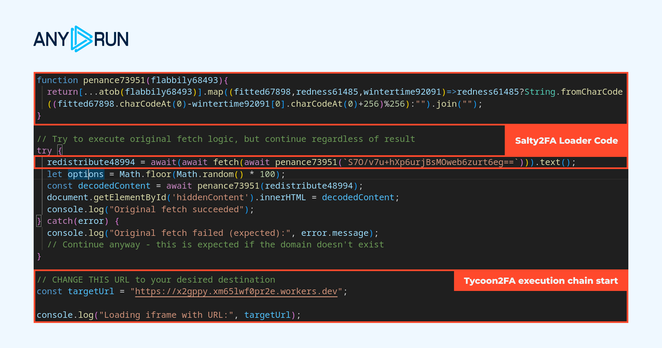
🎣 #Salty2FA relies on encrypted HTTPS communication for fake login pages, redirect flows, and data exfiltration. That’s why it often looks harmless at first glance, delaying confirmation and increasing the risk of credential compromise.
The full phishing flow becomes visible when HTTPS traffic is automatically decrypted in #ANYRUN Sandbox: https://app.any.run/tasks/73fb8a10-2721-4da4-9f9b-a340a6eac370?utm_source=mastodon&utm_medium=post&utm_campaign=salty_ssl_decryption&utm_term=120326&utm_content=linktoservice
👨💻 Learn how #ANYRUN improves phishing detection for SOC teams: https://any.run/cybersecurity-blog/automatic-ssl-decryption/?utm_source=mastodon&utm_medium=post&utm_campaign=salty_ssl_decryption&utm_term=120326&utm_content=linktoblog