Why people working on software where something serious is at stake would throw out known gradient to use a code generator + testing is beyond my capacity to understand.
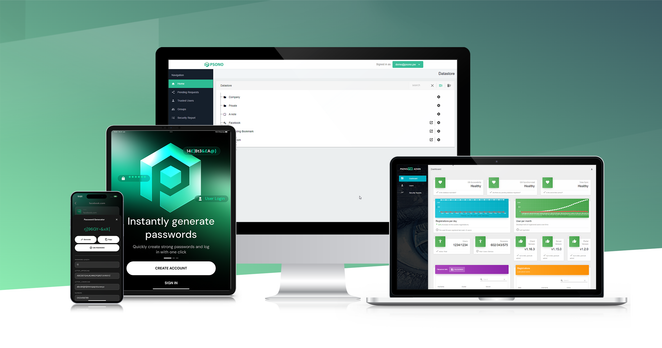
https://1password.social/@1password/116580082041363054
#AI #GenAI #GenerativeAI #LLM #VibeCoding #Software #SoftwareDevelopment #tech #dev #security #InfoSec #PasswordManagers
1Password (@[email protected])
Our engineers used AI-assisted tooling the same way many teams use modern development tools: to help review, organize, and improve internal code. Every change was reviewed by engineers and went through our standard security and quality processes before being accepted. The security model behind 1Password remains the same. We cannot see the contents of your vault, and neither can anyone else. That has not changed.