Is this website legit? 👉 https://www.macaissedepargnehautsdefrancemerepond.fr/
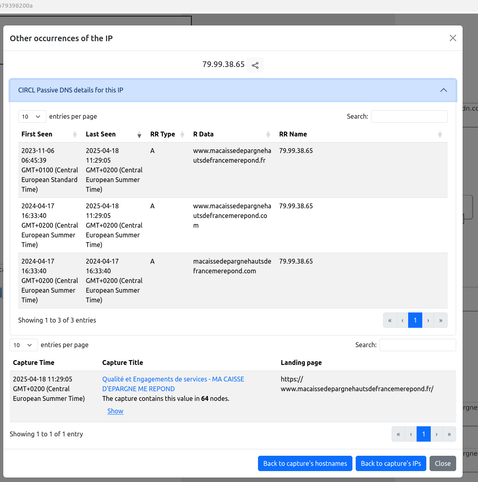
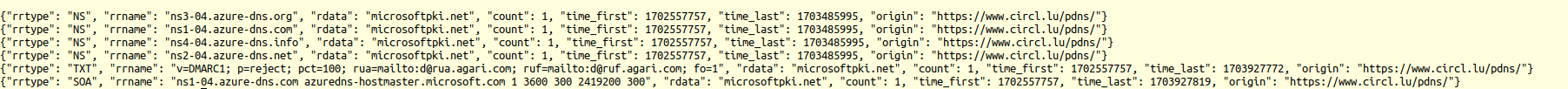
At first glance, the domain name looks suspicious. But when we checked Passive DNS data, it turns out the domain has existed for over two years and has been seen before. Was it taken over, or has it always been active?
Interestingly, there’s no login form on the page, which might suggest it’s not part of a phishing campaign.
So… could it actually be legit? Again PassiveDNS helps a lot but sometime creativity in domain creation makes everything uncertain.
🔗 LookyLoo https://lookyloo.circl.lu/tree/79f3d4f0-3e98-426b-a5df-e4b79398200a