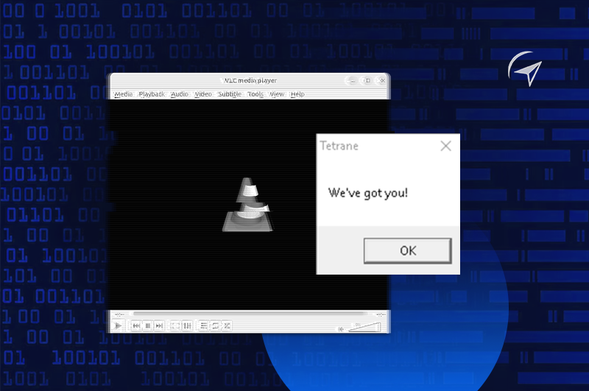
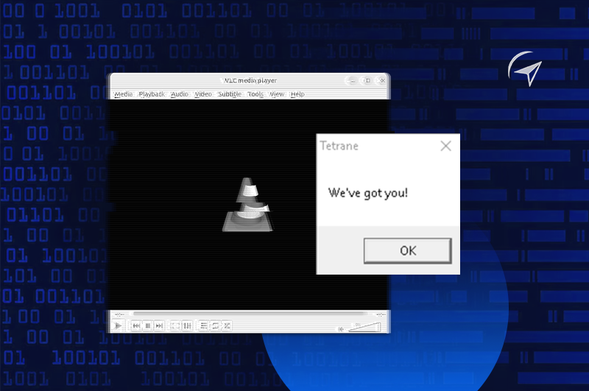
A malicious MKV opens in VLC. A fake calc.exe pops up: "We've got you."
An AI agent made an MCP trace-driven analysis and reconstructed the full exploit chain, use-after-free, heap spray, ROP chain, shellcode, from a single CPU trace.
🔗https://www.eshard.com/blog/vlc-media-player-mkv-exploit-analysis
#exploit #reverseengineering #binary
VLC Media Player MKV Exploit Analysis | eShard
We reconstructed a full VLC Media Player exploit chain from a 4.78-billion-instruction CPU trace using MCP-based time-travel debugging.
Live session with @pqshield: physical attacks on post-quantum crypto, a CPA attack on ML-KEM, and how to harden your defenses.
Limited seats 👇 https://zoom.us/meeting/register/NIX4FovvREe3n6KJ2JbrqA
#pqc #hardware

Welcome! You are invited to join a meeting: Securing Post-Quantum Implementations Against Physical Attacks. After registering, you will receive a confirmation email about joining the meeting.
Quantum-resistant algorithms are arriving in real devices; but physical attacks may already undermine them.
eShard and PQShield explore whether side-channel and fault injection attacks pose a real-world threat to PQC implementations, with a live walkthrough of a CPA attack on ML-KEM and first-step countermeasures.
Speakers:
→ Rafael Carrera Rodriguez, Hardware Security Analyst, eShard
→ Dr Adrian Thillard, Principal Security Analyst, PQShield (ex-Ledger Donjon, ex-ANSSI)
Live, interactive session. Limited capacity — register now.
RE: https://infosec.exchange/@eshard/116527507587211806
Thanks for joining our live! Recording is up at the same link. Just reply here or comment there if you have any questions.

🔴 LIVE: Give Your AI Agent a Time Machine | Reverse Engineering
Join us tomorrow! We'll go live to talk about AI, reverse engineering, time travel debugging, and more: https://youtube.com/live/RaZrX0PX4kI
🔔 Click the bell so you don't miss it!
#ai #reverseengineering #cybersecurity

🔴 LIVE: Give Your AI Agent a Time Machine | Reverse Engineering
Copy.fail is a new Linux kernel privilege escalation vulnerability sitting undetected since 2017, and it has been discovered using AI.
We analyzed it the same way. Locally.
🔗 https://www.eshard.com/blog/copy-fail-internal-llms #Linux #CVE #AI
Copy.fail: Why Internal LLMs Are Non-Negotiable for Security | eShard
We break down the Copy.fail exploit and explain why on-premise AI models are non-negotiable for security teams.
Join us next week for an open conversation about the role of AI in reverse engineering:
🔴 https://www.youtube.com/live/RaZrX0PX4kI
🔔 Click the bell so you don't miss it!
#ai #reverseengineering #cybersecurity

🔴 LIVE: Give Your AI Agent a Time Machine | Reverse Engineering
AI can work great at static analysis, but it fails at at dynamic analysis because runtime data is a moving target.
The only way to solve this is to change the data format: turn dynamic execution into static data.
🔗 https://www.eshard.com/blog/dynamic-analysis-ai-problem #cybersecurity #reversengineering #ai
Turning Dynamic Analysis into an AI Problem | eShard
Dynamic analysis is too unpredictable for AI models. Discover how turning dynamic execution into structured TTD traces solves the data problem.
Last seats for our #TyphoonCon 2026 training in Seoul! 🇰🇷
𝗗𝗲𝗲𝗽 𝗗𝗶𝘃𝗲 𝗶𝗻𝘁𝗼 𝗔𝗻𝗱𝗿𝗼𝗶𝗱 𝗕𝗶𝗻𝗱𝗲𝗿
🗓️ May 27 - 29
Register for this training and get a FREE main conference pass! Reply to claim.
🔗 http://www.eventbrite.com/e/1968561639857/?discount=eShard_sponsors
#reverseengineering #AndroidSecurity #cybersecurity
TyphoonCon 2026
TyphoonCon is an all Offensive Security Training & Conference focused on offensive security, vulnerability discovery and reverse engineering
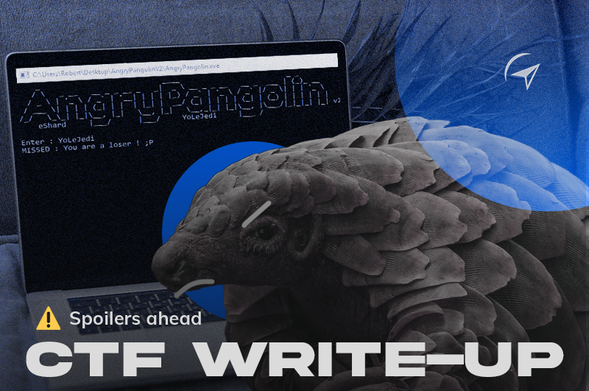
We built a CTF challenge designed to be painful to reverse engineer. Then an AI agent solved it in 6 minutes.
Try it yourself before reading how 👉 https://ttd.eshard.com
Full write-up: https://www.eshard.com/blog/ring0-ring3-key-validator-time-travel-debugging
#CTF #reverseengineer #hacking