Many people have never heard of P2P file-sharing networks like DarkMX even though DarkMX and its predecessor, WinMX, have over two decades of continued development. P2P file-sharing networks are more stable than torrents. DarkMX has a very slick retro interface. It is almost identical to the old WinMX from 20+ years ago, except it brokers all connections via TOR for preserving privacy.
I figured out several ways to run DarkMX on a headless server without GUI. This allows me to install it on a remote server without any desktop environment and run the software as a daemon without the GUI.
First I used the X forwarding feature of SSH to pipe the GUI to a local machine. On that machine I did all the configuration inside the GUI. Then I closed the program.
Then on the remote machine I used 'xvfb' to run DarkMX as a nohup'd daemon with a dummy GUI buffer. That way I don't need to be connected to the GUI from a local machine and the application will still run. It also uses less RAM without the GUI.
There are other ways to do this, such as VNC and xpra. I just chose the quickest, dirtiest method in this case.
Why would I go to all that trouble? Well, I don't need to, but there are some people who might need to publish while maintaining strict anonymity. So they would need tools like DarkMX and TOR. For me it's just fun.
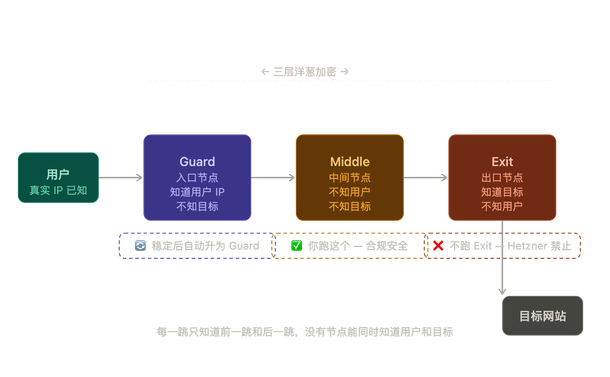
DarkMX operates over the TOR privacy preserving network. As a result the location of my peer is hidden and extremely hard to impossible for an adversary to locate. So when I publish something, such as a letter, or paper, or opinion, anyone can download it since censoring it is not viable. It ensures that my speech remains free and available to the general public. Now when I author essays, papers, homiles and such, I can publish them as file shares, and I can publish them simultaneously as a TOR hidden website with the built-in webserver feature. So readers don't need DarkMX to read my files--they can just fire up TOR Browser or use a TOR proxy with their web browser. If they want to snarf a whole directory they can install DarkMX, or use a script to snarf them via TOR.
If you are inclined to fiddle around with installing this software on a headless server, please share the techniques and tools used that suit you.
(DarkMX download site:
https://darkmx.app)
#DarkMX #P2P #FileSharing #Anonymous #SelfHosting #TOR #OnionNetwork #Censorship@[email protected] @[email protected] @[email protected] [email protected]