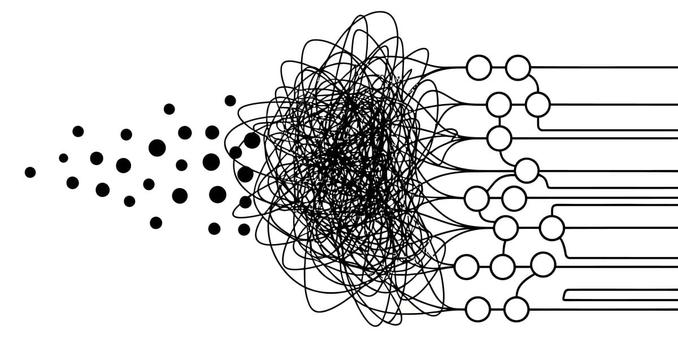
Interesting that a credential compromise can stem from an "agentic OAuth tangle." It just highlights how quickly complexity—especially around identity management and third-party integration—erodes accountability. Interoperability matters, but when these chains get too tangled, data residency and trust become seriously fuzzy. This is complicated stuff…
https://go.theregister.com/feed/www.theregister.com/2026/04/20/vercel_context_ai_security_incident/