#ESETresearch discovered and named 🇨🇳 China-aligned #APT group #PlushDaemon who did a supply-chain compromise of a 🇰🇷 South Korean #VPN provider, trojanizing its legitimate software installer with a Windows backdoor we named #SlowStepper.
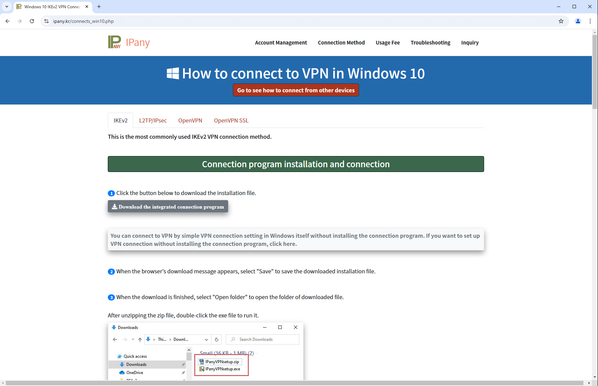
The website had been compromised by PlushDaemon since at least November 2023, resulting in users from 🇰🇷 South Korea, 🇨🇳 China, and 🇯🇵 Japan downloading the trojanized installer, which deployed the legitimate software and SlowStepper.
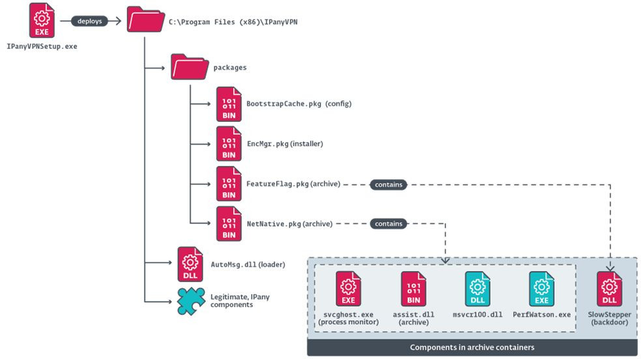
The installer deploys malicious files that contain several components inside a custom-formatted archive , including loaders, a process monitor , legitimate PE files abused for side-loading, and the SlowStepper backdoor.
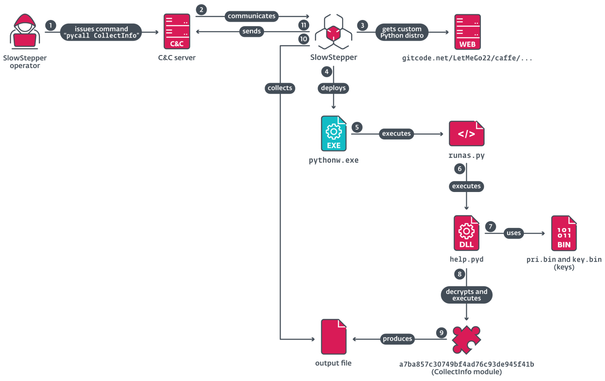
SlowStepper has several interesting features such as decoding #DNS TXT records of a malicious domain to obtain its C&C servers, and a 🐚 shell mode with custom commands, one of which executes modules of an extensive toolkit stored at the Chinese code repository #gitcode
We presented about #PlushDaemon at #jpcert_ac on January 22, 2025 at https://jsac.jpcert.or.jp/
IoCs available in our GitHub repository at https://github.com/eset/malware-ioc/tree/master/PlushDaemon