Proven Cyber Security Recommendations for the Holiday Season
According to research, Cyberattacks increase by 40% in holiday periods. Follow these Holiday Cyber Security Best Practices and Safeguard your Organization from Hackers.
Dive into the depths of SHA-256! Uncover its inner workings, learn how it #safeguards everything and discover its crucial role in upholding trust online - https://certera.com/blog/sha-256-algorithm-know-everything-about-it
#CyberSecurity #trust #SHA256 #infosec #onlinesecurity #EncryptedFence

What Is SHA-256 Algorithm? Detailed Guide on Cryptographic Hash Algorithm
Learn what is SHA 256 hash algorithm, how it works, what are the applications, how it is used for cryptographic security. Complete guide to know about!

Common SSL/TLS Challenges: Attacks, Vulnerabilities and Solutions
Find here what are common challenges and attacks of SSL/TLS Protocol. How Digital threats SSL can prevents.
Buy SSL Certificates Starts at $2.99/Yr - Trusted CA and Provider - Certera
Buy Cheap SSL Certificates to secure your website and user’s confidential information from Comodo, Sectigo, Certera, GeoTrust, Thawte, RapidSSL and more.

Most Common Types of Cyber Attacks and How to Prevent Them
In today's era, its mandatory to protect yourself and business from cyber attacks. Browse most common cyber attacks and its prevention techniques.
Email Spoofing: Learn the Definition, Get a Real-Life Example, and Discover its Prevention tips!
Don't miss this #article to protect your inbox - https://certera.com/blog/what-is-email-spoofing-detailed-guide
#EmailSpoofing #Cybersecurity #tips #guide #EncryptedFence #email

What Is Email Spoofing? Definition, Work, Example & Prevention
Email spoofing is the threat of email messages with a forged sender address. Learn how email spoofing works, how to identify and prevent email spoofing, its examples and more.

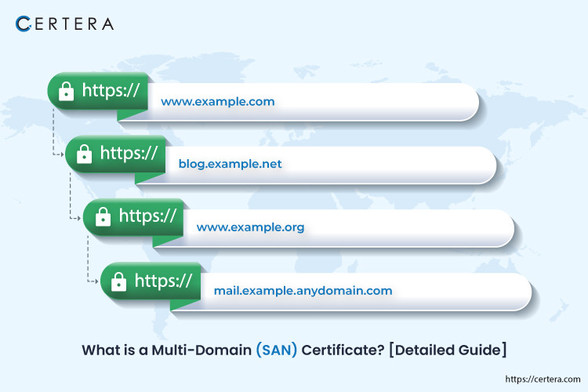
What is the SAN (Subject Alternative Name) SSL Certificate? [Guide]
Understand what is SAN SSL certificate, how it ensure the security of domain names and subdomains, local hostnames, and IP addresses, benefits of multi-domain san SSL.

Hardware Security Modules (HSMs) - Comprehensive Guide
Learn everything about Hardware Security Module (HSM), Types of HSM, Features and Benefits of HSM, Use Cases and more in detail.
Discover the world of Common Vulnerabilities and Exposures (CVEs) in our latest guide!
Learn why they're crucial in #cybersecurity and how they bolster defense against cyber threats 👉 https://certera.com/blog/what-is-common-vulnerabilities-and-exposures-cves-guide
#CVE #InfoSec #guide #cyberthreats #EncryptedFence

Common Vulnerabilities and Exposures (CVE) - Comprehensive Guide
Find here answer of What is CVE common vulnerabilities and exposures, How are CVEs identified, best practices, purpose of CVE and more at once place.

Standard SSL VS Wildcard SSL Certificate: Difference to Know
Discover the key difference between Standard SSL Vs. Wildcard SSL Certificate to choose the appropriate SSL for your business.