#ESET #DeceptiveDevelopment #malware #furtocriptovalute #cybersecurity http://dlvr.it/TNnfNp
#ESET #DeceptiveDevelopment #malware #furtocriptovalute #cybersecurity http://dlvr.it/TNnfNp
#ESET #ESETAPTReport #cybersecurity #DeceptiveDevelopment #infrastrutturecritiche http://dlvr.it/TL6LHM
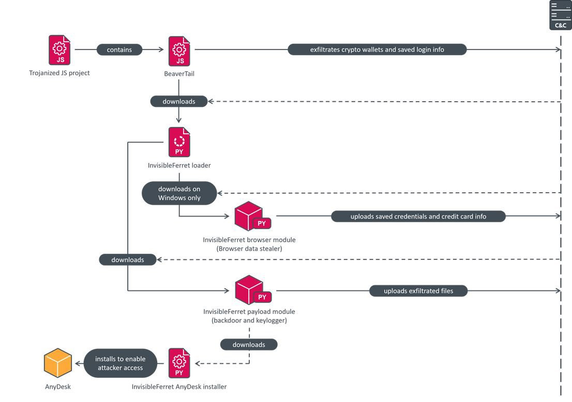
#ESETresearch analyzed a campaign by #DeceptiveDevelopment targeting developers with trojanized coding tests. Posing as recruiters, the operators approach their targets on job-hunting platforms, aiming to steal their cryptocurrency wallets and more.
https://www.welivesecurity.com/en/eset-research/deceptivedevelopment-targets-freelance-developers/
DeceptiveDevelopment is a 🇰🇵-aligned activity cluster. The attackers target software developers on 🪟 Windows, 🐧Linux, and 🍎 macOS, regardless of geographical location, in order to maximize profits.
The campaign primarily uses two malware families – the first, 🦫 BeaverTail, acts as a simple login stealer, extracting browser databases containing saved logins, and is a downloader for the second stage, InvisibleFerret.
InvisibleFerret is modular 🐍 Python-based malware that includes spyware and backdoor components, and is also capable of downloading the legitimate AnyDesk remote management and monitoring software for post-compromise activities.
While DeceptiveDevelopment’s toolset has already been analyzed by https://x.com/Unit42_Intel and https://x.com/GroupIB_TI, our analysis contains details that have not been publicly reported before.
You can find the IoCs in our GitHub repo:
https://github.com/eset/malware-ioc/tree/master/deceptivedevelopment