📢 État de la migration post-quantique des protocoles réseau et sécurité largement déployés
📝 ## 🔬 Contexte
Publié le 30 mars 2026 sur arXiv (cs.NI), cet article académique de Tushin Mallick, Ashish Kundu et Ramana Kompella constitue une **étude de synthèse (su...
📖 cyberveille : https://cyberveille.ch/posts/2026-04-05-etat-de-la-migration-post-quantique-des-protocoles-reseau-et-securite-largement-deployes/
🌐 source : https://arxiv.org/abs/2603.28728
#BGP #DNSSEC #Cyberveille
État de la migration post-quantique des protocoles réseau et sécurité largement déployés
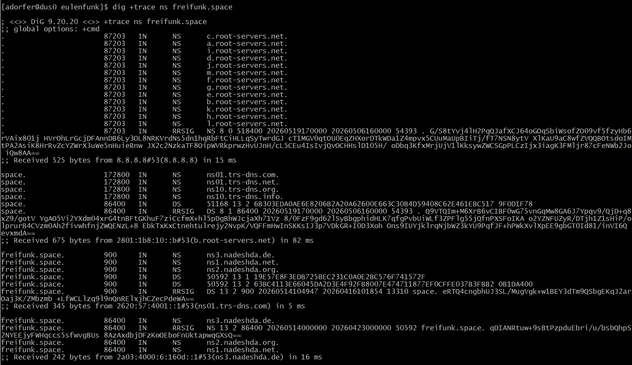
🔬 Contexte Publié le 30 mars 2026 sur arXiv (cs.NI), cet article académique de Tushin Mallick, Ashish Kundu et Ramana Kompella constitue une étude de synthèse (survey) sur l’état de préparation post-quantique des protocoles réseau et de sécurité les plus répandus. ⚠️ Menace identifiée L’émergence de l’informatique quantique représente une menace structurelle pour les primitives cryptographiques à clé publique classiques, notamment : RSA Cryptographie sur courbes elliptiques (ECC) Ces primitives sont au cœur des mécanismes d’échange de clés et d’authentification de la majorité des protocoles réseau critiques.