Who was behind Shadow Brokers?
The answer isn't publicly known.
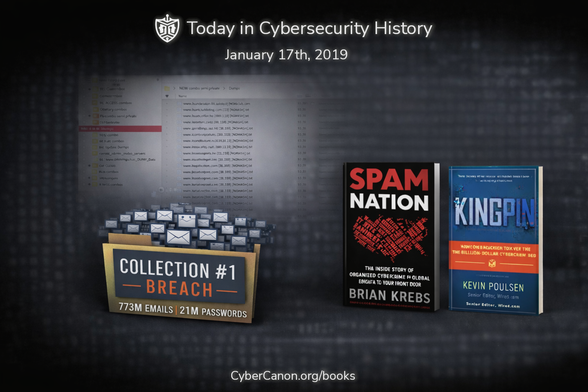
📜 𝗧𝗼𝗱𝗮𝘆 𝗶𝗻 𝗖𝘆𝗯𝗲𝗿𝘀𝗲𝗰𝘂𝗿𝗶𝘁𝘆 𝗛𝗶𝘀𝘁𝗼𝗿𝘆 | 𝗝𝗮𝗻𝘂𝗮𝗿𝘆 𝟭𝟳, 𝟮𝟬𝟭𝟵
Seven years ago today, Troy Hunt ( @troyhunt ) disclosed Collection #1, one of the largest known aggregations of breached credentials at the time.
👉 See Troy's original write-up on this finding: https://www.troyhunt.com/the-773-million-record-collection-1-data-reach/
Collection #1 showed how old breaches become new threats at scale when data is reused, automated, and repackaged. For deeper context on why this happens, we recommend two #CyberCanonHoF books published years before this incident.
𝙎𝙥𝙖𝙢 𝙉𝙖𝙩𝙞𝙤𝙣 - the economics of stolen data ( @briankrebs )
📝 Review: https://cybercanon.org/spam-nation/
🛍️ Amazon affiliate link: https://amzn.to/4o0m5wz
𝙆𝙞𝙣𝙜𝙥𝙞𝙣 - how cybercrime gets monetized ( @Kpoulsen )
📝 Review: https://cybercanon.org/kingpin-how-a-hacker-took-over-the-billion-dollar-cybercrime-underground/
🛍️ Amazon affiliate link: https://amzn.to/4nWQCv4
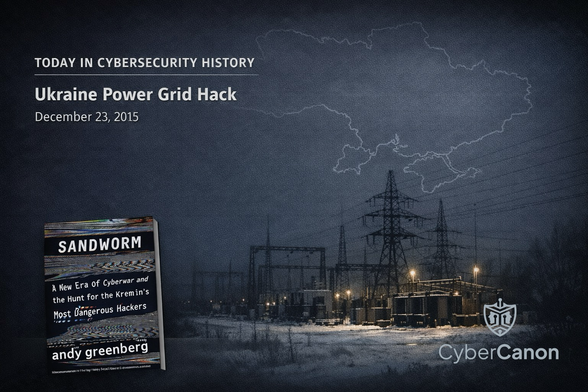
⚡ 𝗧𝗼𝗱𝗮𝘆 𝗶𝗻 𝗖𝘆𝗯𝗲𝗿𝘀𝗲𝗰𝘂𝗿𝗶𝘁𝘆 𝗛𝗶𝘀𝘁𝗼𝗿𝘆 – 𝗗𝗲𝗰𝗲𝗺𝗯𝗲𝗿 𝟮𝟯, 𝟮𝟬𝟭𝟱
On a cold December evening in Ukraine, the lights began to go out.
Not because of a storm or a fallen transmission line. But because an unseen adversary, who was patient, disciplined, and already deep inside Ukraine’s networks, made its move.
Inside three regional power companies, operators watched helplessly as their mouse cursors began to move on their own. Breakers opened. Substations went dark. And within minutes, 230,000 people were without power.
It was the world’s first confirmed blackout caused by a cyberattack.
In Sandworm, Andy Greenberg follows the trail back to the group behind it. An elusive GRU team whose operations would ripple across the globe. What makes this moment unforgettable isn't just the technical achievement of penetrating industrial control systems…
It’s that December 23rd proved a new reality: code could now disrupt cities, societies, and the physical world itself.
Greenberg’s investigative storytelling captures the tension, the human impact, and the geopolitical stakes behind an attack that forever changed how we think about cyberwar.
📘 Cybersecurity Canon Hall of Fame winner,
𝙎𝙖𝙣𝙙𝙬𝙤𝙧𝙢: 𝘼 𝙉𝙚𝙬 𝙀𝙧𝙖 𝙤𝙛 𝘾𝙮𝙗𝙚𝙧𝙬𝙖𝙧 𝙖𝙣𝙙 𝙩𝙝𝙚 𝙃𝙪𝙣𝙩 𝙛𝙤𝙧 𝙩𝙝𝙚 𝙆𝙧𝙚𝙢𝙡𝙞𝙣’𝙨 𝙈𝙤𝙨𝙩 𝘿𝙖𝙣𝙜𝙚𝙧𝙤𝙪𝙨 𝙃𝙖𝙘𝙠𝙚𝙧𝙨:
https://cybercanon.org/sandworm-a-new-era-of-cyberwar-and-the-hunt-for-the-kremlins-most-dangerous-hackers/
#CybersecurityBooks #CybersecurityHistory #CyberWar #OTSecurity (re-added pic…)
🎯𝗧𝗼𝗱𝗮𝘆 𝗶𝗻 𝗖𝘆𝗯𝗲𝗿𝘀𝗲𝗰𝘂𝗿𝗶𝘁𝘆 𝗛𝗶𝘀𝘁𝗼𝗿𝘆: 𝗧𝗵𝗲 𝗧𝗮𝗿𝗴𝗲𝘁 𝗗𝗮𝘁𝗮 𝗕𝗿𝗲𝗮𝗰𝗵, 𝗗𝗲𝗰𝗲𝗺𝗯𝗲𝗿 𝟭𝟵, 𝟮𝟬𝟭𝟯
It started quietly, days before the holiday rush. Shoppers were filling stores, credit cards were swiping nonstop, and behind the scenes, a small foothold inside Target’s network was about to become one of the most infamous breaches in retail history.
💀 Attackers slipped in through a third-party HVAC vendor
🪲 Malware moved silently across point-of-sale systems
💳 40 million payment cards skimmed
🔏 70 million customers' data exposed
While many are (sadly) becoming numb to breach news nowadays, this disclosure, announced 12 years ago today, shook the industry. Boardrooms across the globe were confronted with the fact that cybersecurity wasn’t just an IT problem, but a critical business-wide issue.
The incident is covered very nicely in this Huntress article: https://www.huntress.com/threat-library/data-breach/target-data-breach
Many books in the #CyberCanon address themes related to the breach. Here are two recos to get you started:
𝙉𝙖𝙫𝙞𝙜𝙖𝙩𝙞𝙣𝙜 𝙩𝙝𝙚 𝘿𝙞𝙜𝙞𝙩𝙖𝙡 𝘼𝙜𝙚 discusses cyber risk at the board/executive level and uses high-profile cases to illustrate governance, risk oversight, and leadership implications. Our review📝: https://cybercanon.org/navigating-the-digital-age-the-definitive-cybersecurity-guide-for-directors-and-officers/
𝙏𝙝𝙚 𝘾𝙄𝙎𝙊 𝙋𝙡𝙖𝙮𝙗𝙤𝙤𝙠 is your go-to for structured guidance on integrating 3rd party risk into enterprise security strategy. Our review📝: https://cybercanon.org/the-ciso-playbook/
On November 24, 2014, Sony Pictures Entertainment experienced a landmark cyber-attack. A hacker group calling itself the “Guardians of Peace” unleashed destructive malware, wiped large portions of the studio’s network, and dumped terabytes of sensitive internal data.
𝘾𝙮𝙗𝙚𝙧 𝙒𝙖𝙧𝙨: 𝙃𝙖𝙘𝙠𝙨 𝙏𝙝𝙖𝙩 𝙎𝙝𝙤𝙘𝙠𝙚𝙙 𝙩𝙝𝙚 𝙒𝙤𝙧𝙡𝙙, by Charles Arthur, covers this pivotal event amongst other cyber attacks.
See our review 👉 https://cybercanon.org/cyber-wars-hacks-that-shocked-the-world
#CybersecurityHistory #SonyHack #CyberWar #CybersecurityBooks
📅𝗧𝗼𝗱𝗮𝘆 𝗶𝗻 𝗖𝘆𝗯𝗲𝗿𝘀𝗲𝗰𝘂𝗿𝗶𝘁𝘆 𝗛𝗶𝘀𝘁𝗼𝗿𝘆!
On November 2, 1988, the Morris Worm became the first major computer virus to spread across the Internet. What began as a graduate student’s “experiment” quickly spiraled out of control, taking down much of the early Internet and costing millions in cleanup. It also gave rise to one of cybersecurity’s most important realizations: even well-intentioned code can cause catastrophic damage in a connected world.
To learn more, 𝙁𝙖𝙣𝙘𝙮 𝘽𝙚𝙖𝙧 𝙂𝙤𝙚𝙨 𝙋𝙝𝙞𝙨𝙝𝙞𝙣𝙜 by Scott Shapiro, a #CyberCanonHoFCandidate, covers the #MorrisWorm as one of its five infamous hacks. See our review ➡️ https://tinyurl.com/r2b3zc2u
💥And as a bonus, many may not be aware that 𝙏𝙝𝙚 𝘾𝙪𝙘𝙠𝙤𝙤'𝙨 𝙀𝙜𝙜 also contains an interesting perspective on the Morris Worm. A year after astronomer Cliff Stoll's spy tracking journey, he was one of many admins around the country who were investigating the Morris Worm live as it was spreading through the night. Cliff writes about this experience in the book's epilogue, where he discovers that the author of the worm was actually the son of NSA's Chief Scientist, Robert Morris, whom Cliff worked with in relation to his international hacker sleuthing a year earlier.
#CyberCanonHoF review ➡️ https://tinyurl.com/3rywf7zw
Did you know?
The first computer worm, 'Creeper', appeared in 1971. It moved across ARPANET, leaving a message in it's wake. Cybersecurity was born from this experiment.
🏷️ #90sTech #RetroComputing #VintageSoftware #OldSchoolTech #TechNostalgia #MSDOS #CybersecurityHistory