🚀 CertiK, das Web3‑Security‑Startup, plant einen Börsengang – Ziel: ca. 2 Mrd USD Bewertung.
🔑 *Key Insight*: Durch den IPO will das Unternehmen öffentliches Kapital erschließen, um seine Forschung & globale Expansion zu pushen – ein Schritt, der die Dezentralisierung stärkt, aber den Markt gleichzeitig zentralisiert.
#Web3 #Dezentralisierung #CryptoSecurity #Börse #Privatsphäre
https://www.squaredtech.co/ai-crypto-vulnerability-how-claude-found-a-4-year-old-zcash-flaw?fsp_sid=10956
Coinbase freezing $3M tied to Southeast Asia scam networks shows enforcement is moving on-chain. Spot $BTC ETF outflows show institutional liquidity can reverse fast. Spacecoin's Vietnam deal points to DePIN infrastructure demand.
The real lens: Custody, Compliance, Liquidity, and Security!
Source: https://www.coinbase.com/blog/fighting-scams-at-the-source�
#BTC #CryptoSecurity #DePIN #Risk

Pre-IPOs Are Launching on Coinbase, Starting with SpaceX
TL;DR: Coinbase now offers pre-IPO perpetual futures, giving eligible traders outside the US price exposure to private companies before they go public. Our first listing is the SpaceX Pre-IPO Perpetual Future: USDC-settled, 24/7, no expiry. When SpaceX IPOs, it automatically transitions to the SpaceX Perp with no rollover needed.
تُظهر آخر أخبار DeFi أنه ليس كل الجسور آمنة بعد.
- استغلال Kelp على DAO Bridge تسبب في انخفاض Aave في جلسة متقلبة
- أثر التداول غير المصرح به على الثقة ومعدل العرض/الطلب
- الذراع الواسعة للغموض التقني يبرز أهمية بروتوكولات الأمان
المستثمرون يجب أن يبقوا على علم بالثغرات وأن يعتنقوا تدابير الحماية الموزعة.
Check out today's BlockMap blog article " Avoiding Scams and Staying Safe in the Crypto Space":
https://blockmap.one/blog/avoiding-scams-and-staying-safe-in-the-crypto-space/

Avoiding Scams and Staying Safe in the Crypto Space 🔹 BlockMap
Cryptocurrency has created exciting opportunities for financial freedom, online communities, decentralized applications, gaming, NFTs, and global payments. But as the crypto industry continues to grow, so does the number of scams targeting newcomers and experienced users alike.
🚨 اختراق بروتوكول Squid Crypto وسرقة 3 ملايين دولار
🔍 أهم معلومة: الحادث حدث بعد دعم بروتوكول Ripple، ما يثير تساؤلات حول صلاحية الاعتماد على خدمات تجارية داخلية دون تدقيق كافٍ.
- تدقيق كود غير كافٍ ⇒ ثغرة
- سياسات الأمان غير معتمدة على اللامركزي
- التفاعل السريع مع الموردين ضروري
يجب مراجعة بروتوكولات اللامركزية لضمان عدم إعادة الخطأ. 🌐🔐
#SquidCrypto #Ripple #Decentralization #PrivacyFirst #CryptoSecurity
Crypto drainer alert 🚨
- A “crypto drainer” hijacks wallets via malicious contracts, phishing or weak key storage.
- Look out for unexplained withdrawals, sudden permission requests, or odd contract calls.
- Protect yourself: verify every transaction, keep keys offline, and monitor activity regularly.
#cryptosecurity #privacy #decentralization #wallets #infosec
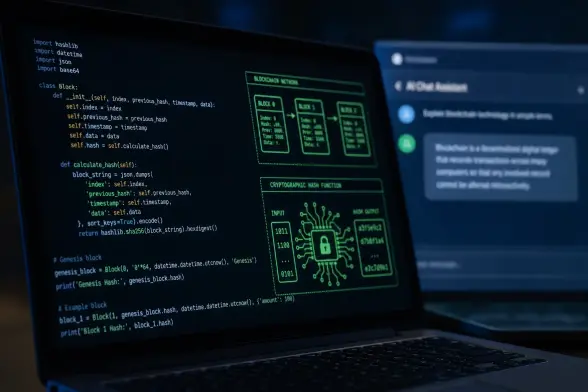
Buterin (Ethereum Founder) suggests that AI-assisted “formal verification” could help secure crypto networks, smart contracts, and cryptographic systems against software flaws.
“If you formally verify end-to-end, then you are proving not just that some description of the protocol is secure in theory, but that the specific piece of code that the user runs is secure in practice." https://decrypt.co/368226/ethereum-founder-vitalik-buterin-ai-verification-secure-crypto-networks #Crypto #CryptoSecurity #Ethereum #BlockChain #Buterin #AI #Verify #SmartContracts #Cryptography #Software #Security #SoftwareBugs
Bitcoin Depot filing Chapter 11 is a warning shot for cash-to-crypto rails. Access is not enough. Crypto infrastructure needs compliance durability, fraud controls, liquidity discipline, and wallet security. Easy UX without resilient controls becomes a liability. #BTC #CryptoSecurity #ObsidianEnochUse
https://www.solo.to/ObsidianEnoch | Architecting the Future of Decentralized Trust
https://cyber.netsecops.io/articles/obsidian-plugin-abused-in-campaign-to-deploy-phantom-pulse-rat/ #ObsidianPlugins #SocialEngineering #CyberSecurity #TechFails #CryptoSecurity #HackerNews #ngated