"the Shai-Halud attack briefly compromised at least 25 NPM code packages managed by CrowdStrike"
Today I read some corporate bullshit on #clownstrike that I can't believe.
Capitalism doesn't work. That company should have exploded. Instead they thrive.
Parody site ClownStrike defended the "obvious" #fairuse.
IT consultant David Senk created ClownStrike in the aftermath of the largest IT outage the world has ever seen—which CrowdStrike blamed on a buggy security update that shut down systems and incited prolonged chaos in airports, hospitals, and businesses worldwide.
https://arstechnica.com/tech-policy/2024/08/parody-site-clownstrike-refused-to-bow-to-crowdstrikes-bogus-dmca-takedown/
https://arstechnica.com/tech-policy/2024/08/parody-site-clownstrike-refused-to-bow-to-crowdstrikes-bogus-dmca-takedown/
Should Clownstrike be held liable? Almost certainly.
Should their developers be held liable?
Probably not, because there is a 99.9% chance they pointed to a pile of tech debt and their management responded with "move fast, break things."
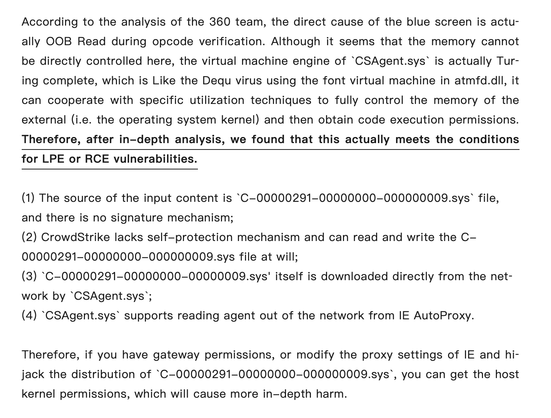
#clownstrike may in fact be the most apt name for the company. Some detailed research over at https://mp.weixin.qq.com/s/uD7mhzyRSX1dTW-TMg4UhQ (via translation tools) has an in depth look at the inner workings of the CSFalcon client and whooo boy.
Key highlights:
- the definition file is not signed or cryptographically validated
- they come straight off the internet via the CSAgent binary
- if you can pwn part of the network stack to point to your file you can mass distribute inside (multiple methods come to mind)
CrowdStrike vs. ClownStrike: Wenn Satire zur Copyright-Farce wird
Die CrowdStrike-Panne, die kürzlich für einen Ausfall zahlreicher Systeme gesorgt hatte, war für Betroffene nicht lustig. Es dauerte nicht lange, bis sich damit jemand einen Spaß erlaubte, darunter die Seite ClownStrike. Doch nicht alle hielten sie für witzig.