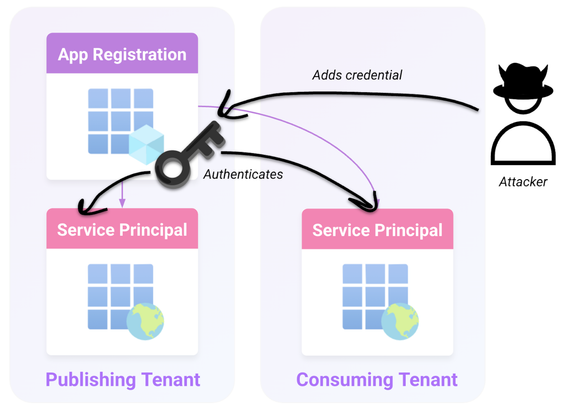
"I SPy" Entra ID Global Admin Escalation Technique
Datadog's Security Labs identified an abuse of Office 365 Exchange Online service principal (SP) allowing escalation to Global Admin. MSRC considers it "expected misconfiguration" so don't expect a fix.
🚨 Alert on new credentials added to SPs.
🔥 Monitor changes to federated domains (federationConfiguration).
🕵🏼♂️ Hunt unusual Graph API calls to /domains, /credentials, and /federationConfiguration.
🔗 https://securitylabs.datadoghq.com/articles/i-spy-escalating-to-entra-id-global-admin/
#DFIR #ThreatHunting #EntraID #CloudForensics #M365 #ThreatDetection