Endlich führt die Uni #WireGuard über #EduVPN ein – und wir sind sehr begeistert! 🎉 Danke an das URZ, dass die Uni aus der #Cisco‑ASA‑Monopol‑Abhängigkeit löst und damit mehr Sicherheit & #Freiheit für uns Studis schafft. Open‑Source‑Lösungen stärken Transparenz und #Unabhängigkeit. 🙏🚀
#ciscoASA #CVE202520333 #CVE202520362 #StaySafeOnline #SecurityAwareness #UniVPN #CampusNetwork #GPLv2 #URZ #AntiMonopoly

CISA aktualisiert Leitfaden zur Sicherheitslage bei Cisco
CISA aktualisiert den Leitfaden zur Cisco-Notfallrichtlinie 25-03: Patchen Sie ASA- und Firepower-Geräte sofort.
China-linked hackers known as Storm-1849 are actively targeting the #Cisco ASA firewall line used by governments and major firms worldwide. Time to patch!
Read: https://hackread.com/china-hackers-target-cisco-firewalls/
#CyberSecurity #InfoSec #CiscoASA #Vulnerability #Hacking

China-Linked Hackers Target Cisco Firewalls in Global Campaign
Follow us on Bluesky, Twitter (X), Mastodon and Facebook at @Hackread
GreyNoise Visualizer | GreyNoise Visualizer
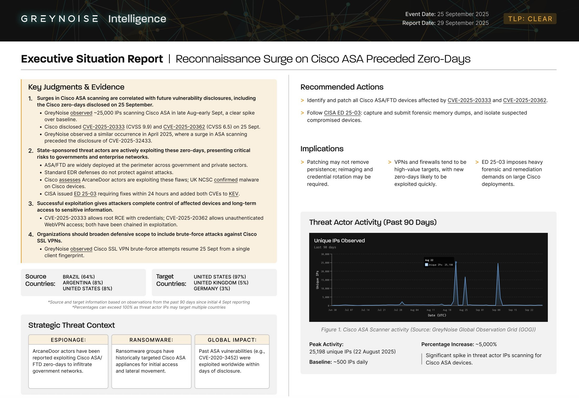
🚨GreyNoise has published a new Situation Report on Cisco ASA reconnaissance activity we observed before the new zero-days were disclosed.
Read the full report: https://info.greynoise.io/hubfs/Situation-Reports/SITREP-Cisco-Zero-Days.pdf
#Cisco #ASA #CiscoASA #GreyNoise #ThreatIntel #CVE202520333 #CVE202520362
Sept 25: Cisco disclosed two ASA/FTD zero-days (#CVE-2025-20333, #CVE-2025-20362).
Weeks earlier, GreyNoise saw 25k IPs scanning ASA — another case of recon surges preceding disclosures.
Read the update: https://www.greynoise.io/blog/scanning-surge-cisco-asa-devices
#CiscoASA #ZeroDay #Cisco

25,000 IPs Scanned Cisco ASA Devices — New Vulnerability Potentially Incoming
GreyNoise observed two scanning surges against Cisco Adaptive Security Appliance (ASA) devices in late August including more than 25,000 unique IPs in a single burst. This activity represents a significant elevation above baseline, typically registering at less than 500 IPs per day.
Cisco ASA devices are under the microscope—over 25,000 IPs from Brazil and beyond are scanning for vulnerabilities. Could this surge be a warning sign for upcoming threats? Dive into the details and see why staying one step ahead is critical.
https://thedefendopsdiaries.com/understanding-the-surge-in-network-scans-targeting-cisco-asa-devices/
#ciscoasa
#networksecurity
#cyberthreats
#vulnerabilitymanagement
#cybersecurity
GreyNoise observed two scanning surges against Cisco ASA devices in late August, both representing significant elevations above baseline. This activity led to the discovery of a botnet cluster solely scanning for Cisco ASA on August 26.
Full analysis: https://www.greynoise.io/blog/scanning-surge-cisco-asa-devices
#CiscoASA #Cisco #GreyNoise #Cybersecurity #ThreatIntel

25,000 IPs Scanned Cisco ASA Devices — New Vulnerability Potentially Incoming
GreyNoise observed two scanning surges against Cisco Adaptive Security Appliance (ASA) devices in late August including more than 25,000 unique IPs in a single burst. This activity represents a significant elevation above baseline, typically registering at less than 500 IPs per day.

Cisco: Angreifer plazieren mithilfe neuer 0-Day-Lücke Hintertüren auf Firewalls
Zwei geschickt gestaltete Hintertüren auf Geräten mit Ciscos ASA- und FTD-System überleben Reboots und Systemupdates. Viele Details sind noch unklar.