RE: https://chaos.social/@icing/116526903529846107
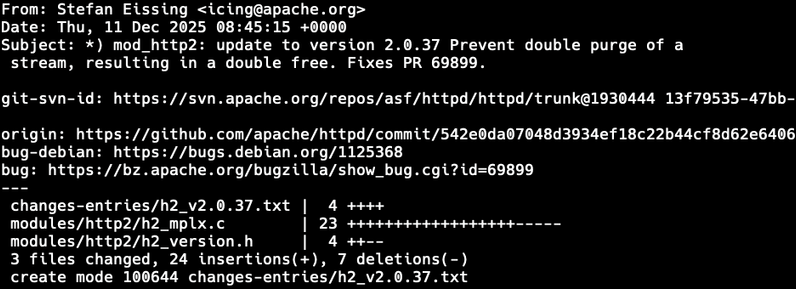
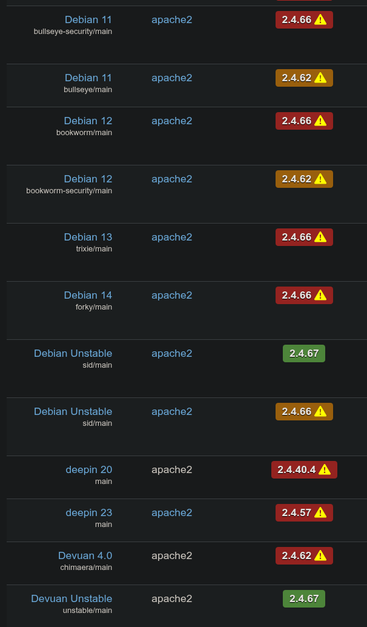
Aftermath: people, running Debian httpd 2.4.66, started complaining when they’ll get the 2.4.67 update to fix this RCE vulnerability. Which they already were protected from, but did not know. Because the CVE was not public at the time the fix was shipped.
[...]
Two security researchers found the vulnerability independently. Just scanning the 2.4.66 source code. This means the bad guys can no longer be kept in the dark. Coordinated disclosure no longer works.