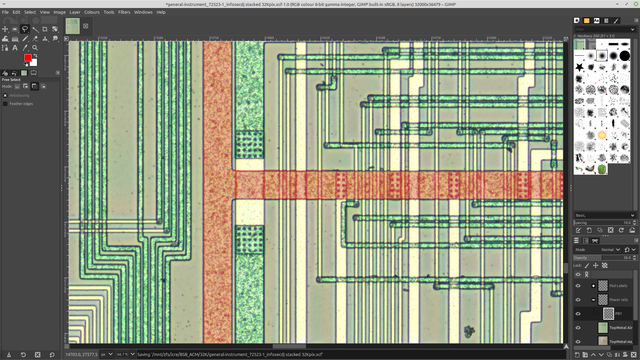
Slow but steady progress on the #BSBACM this evening. Stumbled on two commands in the secure processor firmware which had the same handler code - $0A and $0B.
Turns out they're encryption and decryption functions for IPPV. A 56bit key and 64bit data block go in, a 64bit data block falls out.
The neat bit is it revealed what the crypto hardware does: not the full encrypt/decrypt, but a non-linear function!