op SIDN.nl:
RPKI/ROV-beveiligingsprotocol maakt razendsnelle adoptie door -- Volgende stap is implementatie van ASPA
https://www.sidn.nl/nieuws-en-blogs/rpki-rov-beveiligingsprotocol-maakt-razendsnelle-adoptie-door
Waar RPKI/ROV een heel snelle adoptie heeft doorgemaakt, is het voor de andere twee RPKI-gebaseerde protocollen nog net te vroeg. Wie nu RPKI met ROV heeft draaien, zal een dezer jaren de vervolgstap naar ASPA kunnen maken. Voor BGPsec is het wachten op de volgende generatie routersystemen.
RPKI/ROV-beveiligingsprotocol maakt razendsnelle adoptie door | Cybersecurity | SIDN
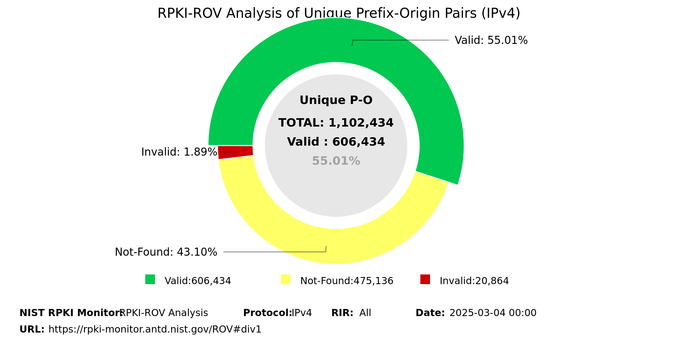
Meer dan de helft van zowel de IPv4- als IPv6-routes in het internetrouteringssysteem BGP is inmiddels beveiligd met RPKI. En belangrijker nog: op dit moment loopt driekwart van al het IP-verkeer naar een RPKI-beveiligde bestemming.