Fake Zoom, Teams Meeting Invites use Compromised Certificates to Drop Malware.
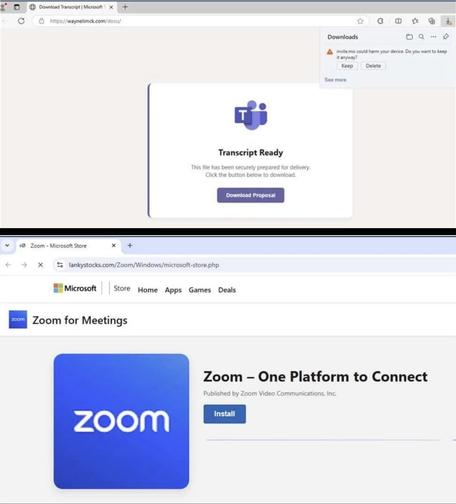
A new wave of phishing attacks is hitting office workers where they feel safest- their daily meeting invites. Instead of using obvious malware, threat actors are now using stolen digital certificates to trick computers into trusting malicious files.
⁉️According to researchers from the Microsoft Defender Security Research Team, these attacks involve highly convincing fake updates for apps like Zoom, Microsoft Teams, and Adobe Reader.⁉️
#zoom #microsoft #teams #adobe #reader #phishing #attacks #rmm #backdoors #it #security #privacy #engineer #media #infosec #tech #news