Email Verification Bypass & AI Credits Manipulation via simple Mass Assignment
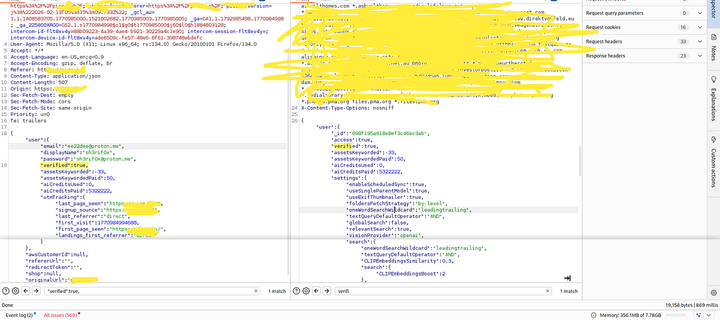
This vulnerability was an Authentication Bypass through a Mass Assignment flaw in the application's registration functionality. The server returned sensitive fields in response to a normal registration request, including verified, aiCreditsPaid, aiCreditsUsed, assetsKeyworded, and settings. By reusing the initial response and modifying sensitive values directly within the request, the researcher bypassed email verification (verified: false ➡️ verified: true), manipulated AI credits (aiCreditsPaid: 50 ➡️ aiCreditsPaid: 5322222, aiCreditsUsed: 0), and controlled multiple internal user attributes. This vulnerability had critical impacts such as bypassing email verification, unlimited AI credits, full control over user internal attributes, and abuse of platform features at scale. The root cause was trusting client-side input, no validation on sensitive fields, and direct binding of request to the user object (Mass Assignment). Proper remediation includes validating sensitive fields, sanitizing user input, and separating bound objects in the application logic. Key lesson: Analyze server responses carefully as they can reveal everything you need to exploit Mass Assignment bugs. #BugBounty #Cybersecurity #WebSecurity #AuthenticationBypass #MassAssignment
https://medium.com/@sh3rif0x/email-verification-bypass-ai-credits-manipulation-via-simple-mass-assignment-60999a81cb4c?source=rss------bug_bounty-5