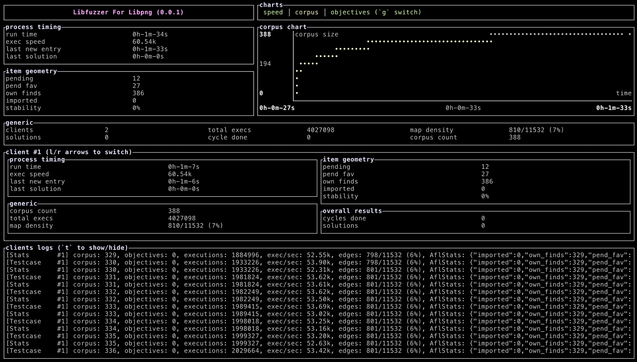
Dipped my toes in #AFLplusplus over the weekend was a kinda nice distraction / pastime.
Got #moarvm (language runtime for #rakulang) its first fuzzing target that exercises the streaming decoder system which is what you would use when reading strings (rather than bytes) with some encoding from a streaming source like the output of a process you're running.
Was a big help to actually put rules in the Makefile to generate the different variants (one with cmplog, one with asan, one with lcov, one with just afl instrumentation) of all the .o files, but I'm not so happy with the rules I came up with.
And to add to the pain, of course there's always nmake which I don't feel like figuring out what exactly I have to do to replace the usage of addsuffix I have ...
https://github.com/MoarVM/MoarVM/pull/1996
If you want to chime in with ideas for what would be good to do with fuzzing in this context, send a comment or toot!
Giving MoarVM its own instrumentation for moarvm bytecode for path coverage would be cool for the future!