@sebsauvage
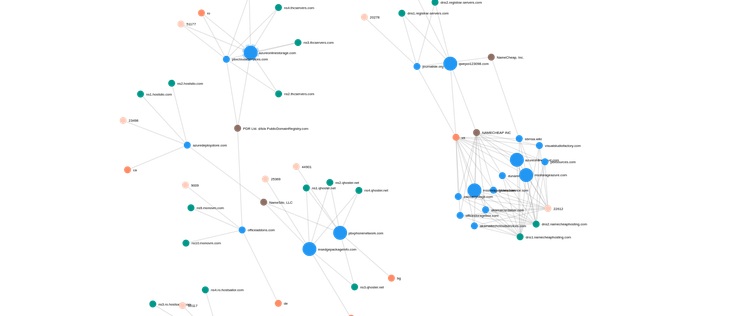
Corruption de la chaîne d'approvisionnement chez l'éditeur de softphone #3cx
Plusieurs utilisateurs indiquent que leurs mot de passe stocke dans leur navigateur ont été volé et utilisé
Les DSI de grosse entreprise comme Pepsi et Mercedes sont très remonté
Le temps de valider l'alerte chez nous, désinstallation en catastrophe de #3cxdesktopapp sur l'ensemble du parc en attendant lundi
#3cxapocalypse
https://www.huntress.com/blog/contextualizing-events-enabling-defense-what-3cx-means