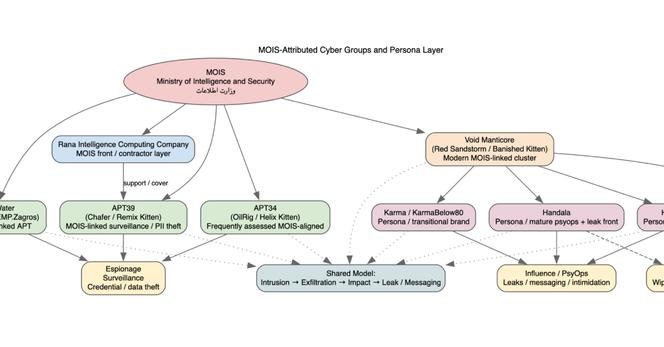
New DTI Research: The evolution of the MOIS-linked cyber ecosystem (Handala/Homeland Justice)
from the 2022 Albania attacks to the 2026 Stryker incident🛡️🇮🇷
Full research and analysis:
https://dti.domaintools.com/research/mois-linked-moist-grasshopper-homeland-justice-karmabelow80-handala-hackers-campaigns-and-evolution#ThreatIntel #Handala #Cybersecurity #Iran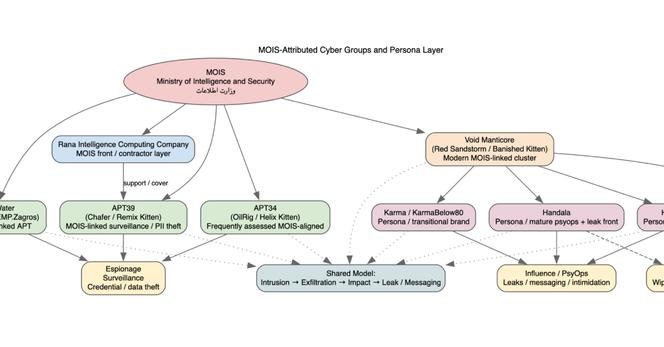
DomainTools Investigations | MOIS Linked MOIST GRASSHOPPER / Homeland Justice / KarmaBelow80 / Handala Hackers / Campaigns and Evolution
Explore the evolution of MOIS-linked actors Homeland Justice, Karma, and Handala. Analysis of destructive malware, surveillance integration, and the 2026 Stryker incident.
How do you make AI work for you in the SOC?
Join our webinar with DomainTools MCP experts Taylor Wilkes-Pierce, VP of Solutions Engineering, and Dan White, VP of Product Management to learn how the MCP server acts as an instant force multiplier.
🔗www.domaintools.com/webinars/supercharging-the-soc-with-domaintools-mcp?utm_campaign=mcpwebinar&utm_medium=social&utm_source=mastadon
📍 Singapore bound for
#BHA2026!
Stop by DomainTools booth # 119 to see how our integrations reduce context-switching and identify evolving threats in real-time.
Don't leave your 2026 strategy to chance. Schedule a chat➡️
https://www.domaintools.com/events/black-hat-asia #BlackHatAsia #CyberSecurity
DomainTools | Black Hat Asia
Spring is here in Seattle🌷, and the March DTI newsletter is live📰.
In this edition Daniel Schwalbe recaps a busy month of research, Ian Campbell's monthly reading list, and where to find us next!
https://dti.domaintools.com/newsletters/fifteen-newsletters-on-a-skateboard
Fifteen (Newsletters) On A Skateboard - DomainTools Investigations | DTI
DTI's March newsletter covers Doppelgänger disinformation infrastructure analysis, Cloudflare-abusing phishing campaigns, a TLS private key exposure in Qihoo 360's AI platform, and a malicious ChatGPT ad blocker Chrome extension stealing user conversations.
Access DomainTools via the Model Context Protocol (MCP) 🌐
Connect your LLM or MCP enabled platform directly to our data to:
✅ Automate data retrieval and analysis
✅ Reduce context-switching
✅ Investigate at the speed of AI
Click here to learn more: https://www.domaintools.ai/mcp-access.
The most critical indicators, all in one place
New enhancements to the DomainTools App for Cortex by Palo Alto Networks deliver real-time streaming of critical intelligence feeds, providing seamless access to DomainTools data across Cortex.
Learn more: https://www.domaintools.com/blog/domaintools-palo-alto-networks-best-in-class-dns-intelligence

DomainTools & Palo Alto Networks: Best in class DNS Intelligence
Learn how DomainTools and Palo Alto Networks Cortex combine best-in-class DNS intelligence with automated playbooks and ML-powered risk scoring to help security teams detect, investigate, and respond to threats faster.
Want to see how the world's best CTI teams map adversary DNS? 🗺️
We’re heading to
#BlackHatAsia 2026 to share how we provide 97% internet visibility and detection 10 days ahead of blocklists.
Let's grab coffee! Book 20 mins here ➡️
https://www.domaintools.com/events/black-hat-asia #BHA2026 #OSINT
DomainTools | Black Hat Asia
🕵️DTI released an analysis of activity attributed to Homeland Justice, Karma/KarmaBelow80, and Handala as a single, coordinated cyber influence ecosystem aligned with Iran’s MOIS.
Read our investigation here:
https://dti.domaintools.com/research/handala-mois-linked-cyber-influence-ecosystem-threat-intelligence-assessment #Cybersecurity #Iran #InfoSec #ThreatIntel
DomainTools Investigations | Handala: MOIS Linked Cyber Influence Ecosystem Threat Intelligence Assessment
Discover how Handala, Homeland Justice, and Karma function as a unified MOIS-linked cyber influence ecosystem. This threat intelligence assessment reveals how Iran uses "hack-and-leak" operations to weaponize perception over technical complexity.
Connecting your LLM to DomainTools is an instant force multiplier ⚡
Analysts get Domain intelligence directly in their chat interface. No context-switching - just natural language answers at the speed of chat.
Technical breakdown & examples ⬇️ https://www.domaintools.com/blog/integrating-domaintools-into-the-ai-powered-soc

Integrating DomainTools into the AI-Powered SOC
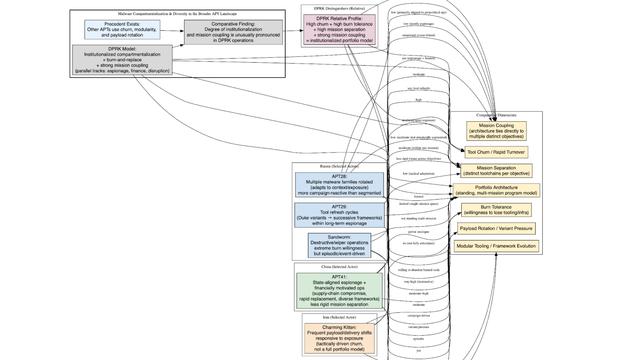
🇰🇵Beyond the Fracture: DomainTools Investigations’ latest research analyzes the fragmented and parallel development pipelines behind North Korea’s specialized malware ecosystem.
Read the research here:
https://dti.domaintools.com/research/dprk-malware-modularity-diversity-and-functional-specialization #Cybersecurity #InfoSec #NorthKorea #Malware #Research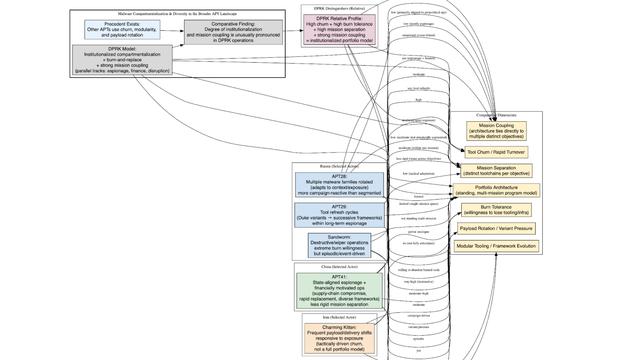
DomainTools Investigations | DPRK Malware Modularity: Diversity and Functional Specialization
Explore the DPRK’s modular malware architecture. Analyze how North Korea uses compartmentalized toolchains for espionage, crypto theft, and strategic signaling.