I wouldn’t normally expect a letterpress reference in a Microsoft security bulletin about a piece of Russian malware, but apparently this one has a pattern of using the word “wayzgoose” in one of its filenames?
The exploit makes use of vulnerabilities in the Windows Print Spooler service, so this makes a kind of sense, but I still find it very surprising.
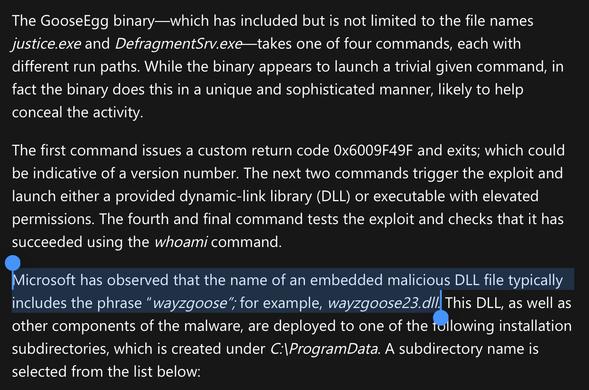
Analyzing Forest Blizzard’s custom post-compromise tool for exploiting CVE-2022-38028 to obtain credentials | Microsoft Security Blog
Since 2019, Forest Blizzard has used a custom post-compromise tool to exploit a vulnerability in the Windows Print Spooler service that allows elevated permissions. Microsoft has issued a security update addressing this vulnerability as CVE-2022-38028.