Why don't we have standardized macaroons yet?
I want to shut down some cloud resource when I'm done with it, but the same API key that lets me do that can also spend my money, so now the thing that does the shutdown has to live in a trusted place.
I could wait for the provider to implement their own permission system which I don't want to learn, or I could just pre-bottle a "I agree to running /shutdown with these parameters between these dates" message and have a dumb thing fire that off.
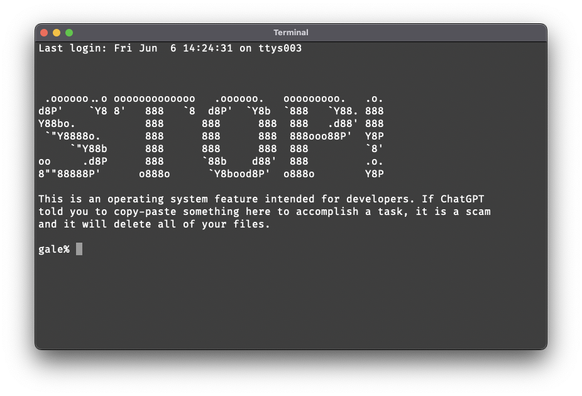
(This message brought to you by [expensive gadget vendor] hard-coding an API token so their device could send emails, but accidentally letting everyone read all emails sent by the company, including password-reset emails and user documents.)