| 🕸 | https://alf.nu/ |
| 🍗 | https://twitter.com/steike |
| [object Object] | https://true.alf.nu/ |
Erling (Alf) Ellingsen
- 141 Followers
- 339 Following
- 70 Posts
The best part came a year later, after the patches were finally out to fix (some of) the issues.
Here's a snippet from the header of a game file.
Can you guess what went wrong?
"I wish people would stop inventing subtly incompatible backslash encodings"
*monkey paw curls*
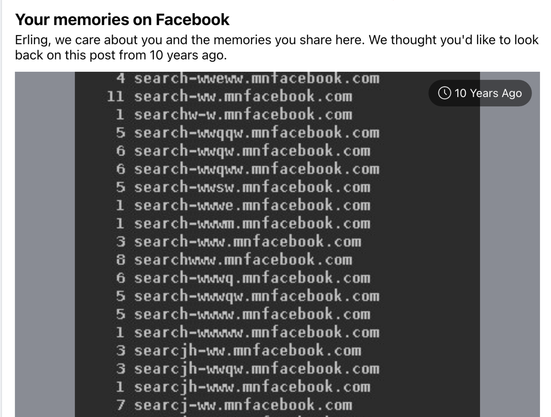
Heh, Facebook popped up this "memory" today.
So a decade ago there was a bunch of postMessage handling code with a regex like /^(m|www).facebook…/, so I grabbed a domain that matched. I picked 'n' for the arbitrary letter, hoping to get a few free lucky bit flips, but then Baidubot hit me with these. Still not sure why. Seeding crawl by DNS logs would necessarily be a surprise, but... even if they did, I don't remember search-www.m.facebook… being a host name that was in use.
OK, that was odd. We're travelling for the holiday, so I figured I'd get ssh running on port 443 in case I ended up behind a dumb middlebox.
(HTTPS is client-first and SSH is either-first, so they can share)
Went to patch my local copy of Warp, found that 2019 me had already done so ... but apparently *also* hit an even more annoying middlebox that would filter any stream starting with 'SSH-', regardless of port?!
There’s hardware support for the INTERCAL squiggle operator '~' now. Not sure how I feel about this.
HT https://mastodon.gamedev.place/@rygorous/109531679136944313
Fabian Giesen (@[email protected])
@[email protected] @[email protected] especially with "trick shot' insns. One example for x64 would be PDEP/PEXT which are really good (1 uop, 3c latency) on Intels and AMD Zen3+ and horrible on Zen1/2 (often 100+ uops) - enough so that you probably want to avoid them on general principle for any code that might see a Zen1/2 ever.
I wanted to call "__html" something more specific, like "THIS_IS_AN_XSS_HOLE" or "DO_NOT_USE_OR_YOU_WILL_BE_FIRED.", but I was concerned about how my boss would handle seeing the inevitable blog post titled "how to find an XSS hole in Facebook: grep for XSS_HOLE".
Then React inherited the name, and now it's everywhere. Not quite Hoare levels of regret, but still not great.
OK, sorry, I guess everyone's tired of the thing, but: IT HAD TO LEARN TO SPELL.
Something like 'morph' enters the model as single token, so in order to be able to do things like case folding or extract ascii values, it has to break it into individual letters by hand. Which it can do. Mostly.
You're gonna make it, Li'l Brudder!