redsakana
- 13 Followers
- 90 Following
- 489 Posts
systemd-in-initramfs (as provided by dracut) is, even by recent systemd standards, an explosion of completely unnecessary complexity.
Emergency shell setup the dracut version that trixie ships generates is completely broken because systemd-sysusers fucks up /etc/shadow. This is apparently fixed in a later dracut version, but no one seems to have an answer as to why systemd-sysusers is needed in initramfs.
(Currently working on switching back to initramfs-tools while keeping LUKS TPM unlock, because this is not the first time I have had problems with systemd-flavored initramfs.)
Threw together an Apparmor profile + zsh integration to automatically run build/package tools confined inside a predefined set of project directories with aa-exec on dev mahines. This won't prevent packages in project A from attacking project B, but should at least keep out garden variety infostealers.
It's a bit of a lost opportunity that AA profiles can't easily be loaded at runtime so you can't just give aa-exec a path to a profile, it has to be preloaded into the kernel. I guess this is where Landlock would shine, but the AA profile language is IMO pretty convenient.
The development process turned up some gems like poetry (Python package tool) going into an infinite retry loop if it gets EACCES on anything.
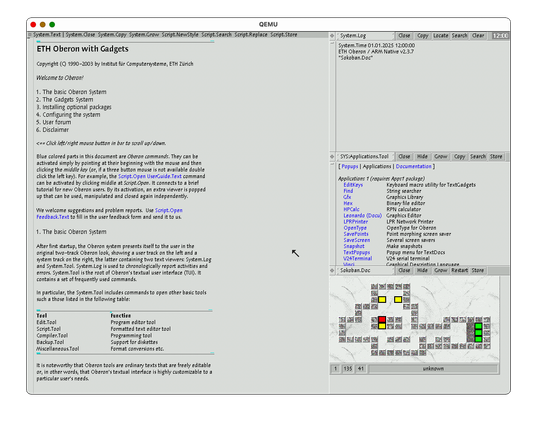
Oberon 3 for ARM (on the screenshot: RPi2) is neat. It is always refreshing to try operating systems and interfaces that live in a completely different paradigm from *nix or win-like. I'm running a pre-release from 11 hours ago.
https://github.com/rochus-keller/OberonSystem3Native/releases
Customer insisted on sharing tens of GB of stuff as a sharepoint folder that they managed to share to an account attached to our 10-years-dormant MS organization.
After fighting with the MS organization thing and a million 2FA prompts for a while, the best that could be done was to get a browser view of the stuff. However it turns out that guessing the WebDAV URL, adding an rclone webdav config with vendor "other" and sticking the FedAuth cookie from the browser session in there was enough to grab the files.
Cookie theft is the best.
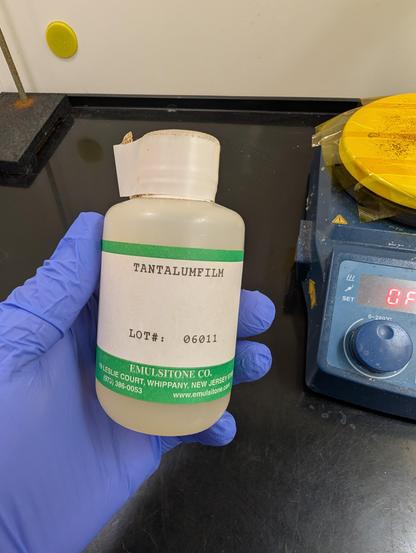
Still as cis as ever, but I thought I'd show my support by posting an interesting transition metal compound from my lab inventory.
Here's a solution of tantalum chloride in ethanol/methanol, intended for sol-gel deposition of tantalum pentoxide thin films. You spin coat it on a substrate then heat in air; the chlorine swaps with an oxygen in atmospheric water vapor and you get HCl gas evaporating and Ta2O5 on the surface.
So to summarize state of Firefox AI garbage group policies:
* ESR (140): Preferences whack-a-mole with browser.ml. flags only.
* Current (149): GenerativeAI policy group should deal with the worst bits, but keeping some Preferences browser.ml. bits around may be needed.
* Upcoming (who knows when, hopefully 150-ish): new AIControls policy group looks like it will deal with more outright badness.
Locking extensions.ml.enabled to false is probably still wise.