Treasury Takes Action Against Major Cyber Scam Facilitator
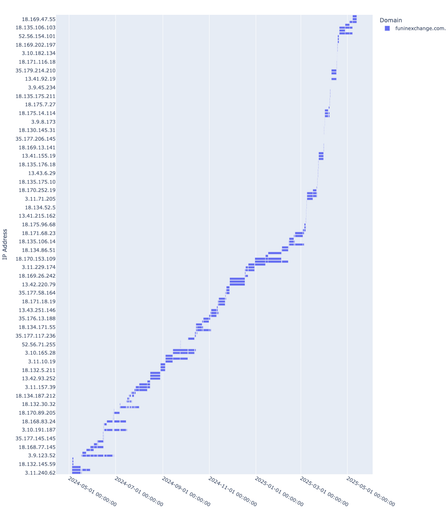
WASHINGTON — Today, the Department of the Treasury’s Office of Foreign Assets Control (OFAC) sanctioned Funnull Technology Inc., a Philippines-based company that provides computer infrastructure for hundreds of thousands of websites involved in virtual currency investment scams, commonly known as “pig butchering,” along with its administrator, Liu Lizhi. Americans lose billions of dollars annually to these cyber scams, with revenues generated from these crimes rising to record levels in 2024. Funnull has directly facilitated several of these schemes, resulting in over $200 million in U.S. victim-reported losses. “Today’s action underscores our focus on disrupting the criminal enterprises, like Funnull, that enable these cyber scams and deprive Americans of their hard-earned savings,” said Deputy Secretary of the Treasury Michael Faulkender. “The United States is strongly committed to ensuring the continued growth of a legitimate, safe, and secure digital asset ecosystem, including the use of virtual currencies and similar technologies.” This action was taken in close coordination with the Federal Bureau of Investigation (FBI). To assist the private sector in identifying and taking down websites associated with Funnull, the FBI is also publishing a cybersecurity advisory with more information on Funnull’s operations, including technical details about the IP addresses and computer infrastructure that it uses. The public is encouraged to report online scams and other illegal online activity to the FBI’s Internet Crime Complaint Center (IC3).SOPHISTICATED CYBER SCAMS TARGETING AMERICANSIn September 2023, the Treasury Department’s Financial Crimes Enforcement Network (FinCEN) published an alert about pig butchering scams. These scams are largely perpetrated by criminal organizations based in Southeast Asia who use victims of labor trafficking to conduct outreach to millions of unsuspecting individuals around the world. The scammers leverage fictitious identities, the guise of potential relationships, and elaborate storylines to deceive victims into believing they are in trusted relationships. The scammers then steal victims’ assets by convincing them to invest in virtual currency through a fake website designed to look like a legitimate investment platform that reflects significant, but fabricated, returns on the investment. However, once a victim is unable or unwilling to pay more into the scam, the scammer will abruptly cease communication, taking the victim’s entire investment with them.FUNNULL’S SUPPORT TO THOUSANDS OF PIG BUTCHERING WEBSITESFunnull Technology Inc. (Funnull) enables virtual currency investment scams by purchasing IP addresses in bulk from major cloud services companies worldwide and selling them to cybercriminals to host scam platforms and other malicious web content. Funnull is linked to the majority of virtual currency investment scam websites reported to the FBI. U.S.-based victims of these scam websites have reported over $200 million in losses, with average losses of over $150,000 per individual. These figures likely underestimate the total losses, as many victims of scams do not report the crime. Funnull generates domain names for websites on its purchased IP addresses using domain generation algorithms (DGAs)—programs that generate large numbers of similar but unique names for websites—and provides web design templates to cybercriminals. These services not only make it easier for cybercriminals to impersonate trusted brands when creating scam websites, but also allow them to quickly change to different domain names and IP addresses when legitimate providers attempt to take the websites down. In 2024, Funnull purchased a repository of code used by web developers and maliciously altered the code to redirect visitors of legitimate websites to scam websites and online gambling sites, some of which are linked to Chinese criminal money laundering operations. Liu Lizhi (Liu), a Chinese national, is an administrator of Funnull. Liu was involved in and possessed spreadsheets and other documents containing information about Funnull’s employees, their performance, and their progress on tasks. These tasks included assigning domain names to cybercriminals, including domains associated with virtual currency investment fraud, phishing scams, and online gambling sites.OFAC is designating Funnull pursuant to Executive Order (E.O.) 13694, as further amended by E.O. 14144, for having materially assisted, sponsored, or provided financial, material, or technological support for, or goods or services to or in support of cyber-enabled activities originating from, or directed by persons located, in whole or substantial part, outside the United States that is reasonably likely to result in, or has materially contributed to, a threat to the national security, foreign policy, or economic health or financial stability of the United States and that has the purpose of or involves causing a misappropriation of funds or economic resources, intellectual property, proprietary or business confidential information, personal identifiers, or financial information for commercial or competitive advantage or private financial gain. OFAC is also designating Liu pursuant to E.O. 13694, as further amended by E.O. 14144, for being owned or controlled by, or having acted or purported to act for or on behalf of, directly or indirectly, Funnull.SANCTIONS IMPLICATIONSAs a result of today’s action, all property and interests in property of the designated or blocked persons described above that are in the United States or in the possession or control of U.S. persons are blocked and must be reported to OFAC. In addition, any entities that are owned, directly or indirectly, individually or in the aggregate, 50 percent or more by one or more blocked persons are also blocked. Unless authorized by a general or specific license issued by OFAC, or exempt, OFAC’s regulations generally prohibit all transactions by U.S. persons or within (or transiting) the United States that involve any property or interests in property of blocked persons. Violations of U.S. sanctions may result in the imposition of civil or criminal penalties on U.S. and foreign persons. OFAC may impose civil penalties for sanctions violations on a strict liability basis. OFAC’s Economic Sanctions Enforcement Guidelines provide more information regarding OFAC’s enforcement of U.S. economic sanctions. In addition, financial institutions and other persons may risk exposure to sanctions for engaging in certain transactions or activities involving designated or otherwise blocked persons. The prohibitions include the making of any contribution or provision of funds, goods, or services by, to, or for the benefit of any designated or blocked person, or the receipt of any contribution or provision of funds, goods, or services from any such person. The power and integrity of OFAC sanctions derive not only from OFAC’s ability to designate and add persons to the Specially Designated Nationals and Blocked Persons List (SDN List), but also from its willingness to remove persons from the SDN List consistent with the law. The ultimate goal of sanctions is not to punish, but to bring about a positive change in behavior. For information concerning the process for seeking removal from an OFAC list, including the SDN List, or to submit a request, please refer to OFAC’s guidance on Filing a Petition for Removal from an OFAC List.Click here for more information on the persons designated today. To report internet crime to the FBI, click here.###