Paul
- 85 Followers
- 187 Following
- 172 Posts
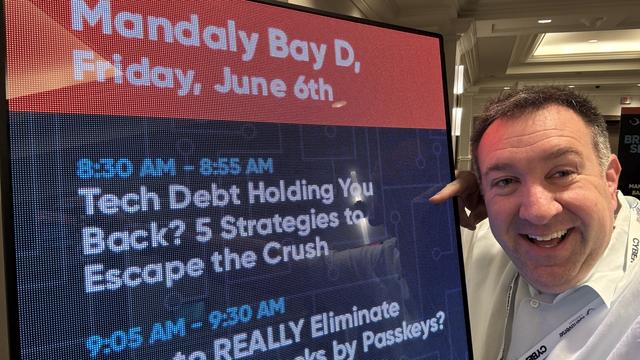
https://events.identiverse.com/2025/on-demand-content
If you're interested in the two sessions I presented, they're both on the Day 4: Friday, June 6 tab.
Great article on our work on the Blast-RADIUS attack by @dangoodin.
One of the most widely used network protocols is vulnerable to a newly discovered attack that can allow adversaries to gain control over a range of environments, including industrial controllers, telecommunications services, ISPs, and all manner of enterprise networks.
Short for Remote Authentication Dial-In User Service, RADIUS harkens back to the days of dial-in Internet and network access through public switched telephone networks. It has remained the de facto standard for lightweight authentication ever since and is supported in virtually all switches, routers, access points, and VPN concentrators shipped in the past two decades. Despite its early origins, RADIUS remains an essential staple for managing client-server interactions.
Since 1994, RADIUS has relied on an improvised, home-grown use of the MD5 hash function. The result is “Blast RADIUS,” a complex attack that allows an attacker with an active adversary-in-the-middle position to gain administrator access to devices that use RADIUS to authenticate themselves to a server.