In the last few days, our SCUMM engine has seen some substantial changes.
Introducing: Partial support for two new games!
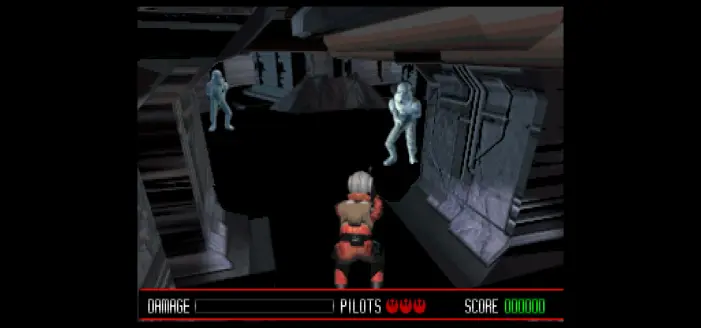
Please welcome "Star Wars: Rebel Assault" and "Star Wars: Rebel Assault II: The Hidden Empire"!
This is still work in progress, so there's no full support - yet.