| Privacy Guides | https://www.privacyguides.org |
| PixelFed | https://pixelfed.social/nathan_wasson |
Nathan Wasson 🇺🇦
- 83 Followers
- 134 Following
- 1.2K Posts
NEW: The FBI said it is investigating a hack on its networks.
The breach affected the FBI's systems to manage wiretaps and surveillace requests, according to CNN.
The Wikimedia Foundation suffered a security incident today after a self-propagating JavaScript worm began vandalizing pages and modifying user scripts across multiple wikis.
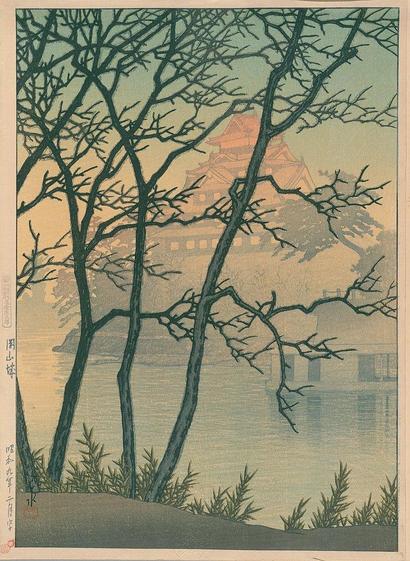
NEW: There have been a few reports and some statements from government officials that suggest cyber operations played a significant role in the first days of the war in Iran.
At the end of the day this war is about dropping bombs, but these reports show cyber can have an important supporting role — for surveillance, intelligence gathering, disruption, and PYOPs — in real world conflict.

Hacked traffic cams and hijacked TVs: How cyber operations supported the war against Iran | TechCrunch
After U.S. and Israeli forces started bombing Iran, reports say cyber operations have disrupted communications, supported surveillance activities, and have been used in psychological operations.
Great article on #Git and some of the changing being made.
While I'm happy to see the transition from SHA-1 to SHA-256, the user interface improvements cannot be understated. Git truly is "use 10% of the tools to complete 90% of the work", largely because it's so damn complicated.