#ghidra #reverseengineering
- 40 Followers
- 9 Following
- 14 Posts
#ghidra #reverseengineering
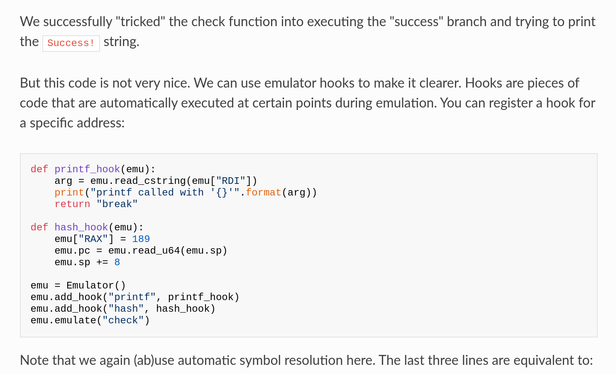
Actually, since the release a week ago, we already got a few new useful features, including:
* Even easier function emulation (`Function("Foo").emulate(1, 2, 3)` will correctly pass the parameters, emulate the call and return the result)
* Built-in patching, assembly, disassembly and searching for byte patterns
* And a parlor trick: instruction/function/things highlighting. `for i in Instruction.all(): if i.mnemonic == "CALL": i.highlight()`
Sorry for the delay, but I'd like to share one of my recent updates:
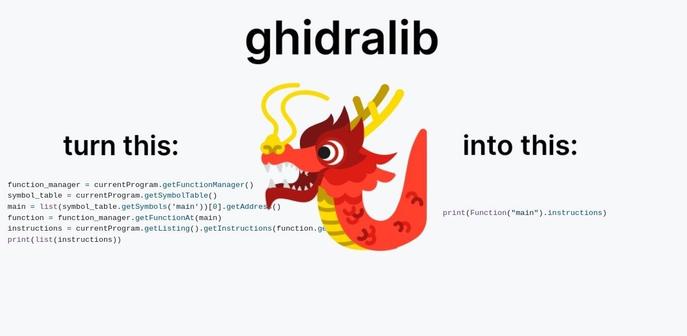
Recently I open-sourced ghidralib - a library that makes #Ghidra scripts drastically shorter and easier to write. I've been using it daily for #reverseengineering and decided it’s time to share. The source code is here: https://github.com/msm-code/ghidralib, and the docs are https://msm-code.github.io/ghidralib/
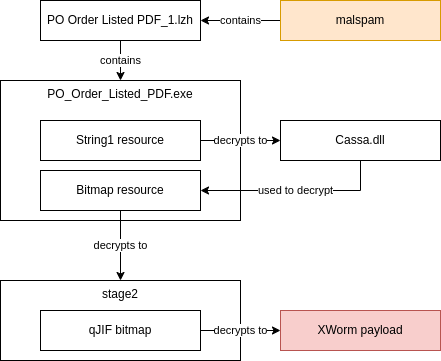
Another blag post about .NET malware (XWorm this time) if that's something you like: https://cert.pl/en/posts/2023/10/deworming-the-xworm/.
It's not a terribly interesting malware family (yet another .NET stealer), but I think reversing it is a good example of unpacking .NET malware automatically and then automating the process. Pretty useful if you want to batch analyse thousands+ samples/day 🙃.
Remember that the default account is *shared* and other users see your jobs. Consider registering a throwaway account (fake email ok).
Oh, and I'm posting this on mastodon before birdsite to ~~manage the load~~ help the fediverse.
Ok, I keep finding things to improve and shaving that yak. I should probably just go ahead and publish this, or this will take forever.
So officially, I've indexed the whole vxunderground's VirusShare collection and created a public service to search all that data: https://mquery.net. If malware is your thing, check it out.
...hello? Is this thing on? Let's try it.
I'm indexing whole vxunderground malware collection, and I'm planning to setup a public and free mquery instance with all the data for everyone to query. Current status: all small (<=1MB) files indexed, compacting the database and then I'll index medium (1<x<4MB) files. ETA for public release is early January.