Sorry for the delay, but I'd like to share one of my recent updates:
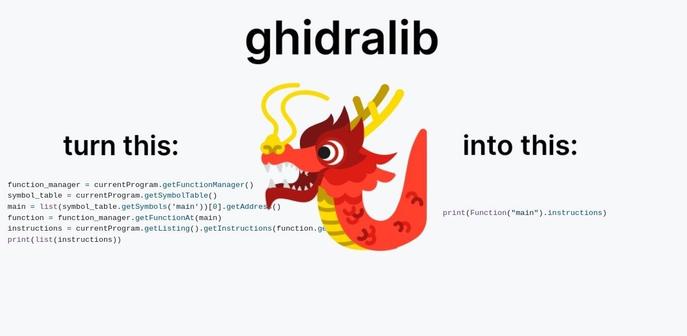
Recently I open-sourced ghidralib - a library that makes #Ghidra scripts drastically shorter and easier to write. I've been using it daily for #reverseengineering and decided it’s time to share. The source code is here: https://github.com/msm-code/ghidralib, and the docs are https://msm-code.github.io/ghidralib/