MattT ✅
- 189 Followers
- 31 Following
- 51 Posts
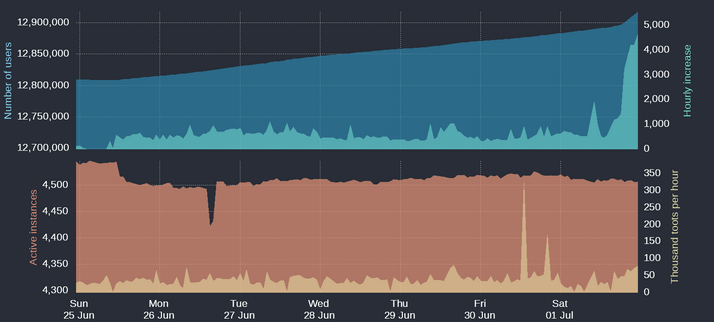
+4,614 in the last hour
+34,484 in the last day
+108,119 in the last week
Researchers have devised a novel attack that recovers the secret encryption keys stored in smart cards and smartphones by using cameras in iPhones or commercial surveillance systems to video record power LEDs that show when the card reader or smartphone is turned on.
The attacks enable a new way to exploit two previously disclosed side channels, a class of attack that measures physical effects that leak from a device as it performs a cryptographic operation. The first attack uses an Internet-connected surveillance camera to take a high-speed video of the power LED on a smart card reader—or of an attached peripheral device—to pull a 256-bit ECDSA key off a government-approved smartcard. The other allowed the researchers to recover the private SIKE key of a Samsung Galaxy S8 phone by training the camera of an iPhone 13 on the power LED of a USB speaker connected to the handset.
Justice Department Announces Court-Authorized Disruption of the Snake #Malware Network Controlled by #Russia's Federal Security Service
Justice Department Announces Court-Authorized Disruption of the Snake Malware Network Controlled by Russia's Federal Security Service
“Russia used sophisticated malware to steal sensitive information from our allies, laundering it through a network of infected computers in the United States in a cynical attempt to conceal their crimes. Meeting the challenge of cyberespionage requires creativity and a willingness to use all lawful means to protect our nation and our allies,” stated United States Attorney Peace. “The court-authorized remote search and remediation announced today demonstrates my Office and our partners’ commitment to using all of the tools at our disposal to protect the American people.”
https://www.govinfosecurity.com/ex-uber-cso-joe-sullivan-avoids-federal-prison-a-21984
The Quad, University of Washington, Seattle, Washington
#Photography #Spring #UW #WashingtonState
photo by Chirayu Desai