#Rust #UA
| Github | https://github.com/marshray |
| Bluesky | @marshray.bsky.social |
| Discord | marshray |
| marshray & live ! c0m | |
| Twitch | https://www.twitch.tv/marsh_ray |
| Type | Static, strict |
| Github | https://github.com/marshray |
| Bluesky | @marshray.bsky.social |
| Discord | marshray |
| marshray & live ! c0m | |
| Twitch | https://www.twitch.tv/marsh_ray |
| Type | Static, strict |
It appears that Andrej Karpathy is challenging Richard Feynman as humanity's leading techno-spiritual philosopher.
(Or so I gather from the thumbnails Youtube offers me in incognito mode. I don't click on any of this.)
ThePrimagen is the most prolific theologian of our age.
I've deduced a law of nature: this universe does not permit more than three screenfuls of vertical space without a recommendation of something involving a DUI traffic stop by cops or a pro se defendant.
There are approximately 488 Linux kernel CVEs per month* and not a lot of reason to think that CVE-2026-31431("copy .fail") is particularly special.
- It's an LPE (local privilege escalation). Yes, we should take it seriously and never give up the dream. No, you should not rely on non-virtualized containers to provide a true multi-tenant security boundary.
- Every potential attacker in the world has been able to observe the vulnerability in source code form since mid-2017 (9 years ago).
https://git.kernel.org/pub/scm/linux/kernel/git/torvalds/linux.git/commit/?id=72548b093ee38a6d4f2a19e6ef1948ae05c181f7
- The vendor was notified of the vulnerability 2026-03-23 (39 days ago), apparently with enough detail to put together a patch in ~3 days.
- Every potential attacker in the world was informed of the specific vulnerability 30 days ago (2026-03-31 at the latest) when the patch was committed with the header "Reported-by: Taeyang Lee <0wn@ theori. io>" Theori .io advertises both offensive and defensive security information services on their site.
https://git.kernel.org/pub/scm/linux/kernel/git/herbert/crypto-2.6.git/commit/?id=a664bf3d603dc3bdcf9ae47cc21e0daec706d7a5
The researchers:
- Notified the kernel security team
- Observed the patch committed
- Waited another 34 days
- Published a detailed writeup
Professionally done, IMO.
The researchers followed the process outlined on the affected vendor's website. Specifically:
"the kernel security team strongly recommends that as a reporter of a potential security issue you DO NOT contact the “linux-distros” mailing list UNTIL...[list that includes some absurdly vague conditions]"
https://docs.kernel.org/process/security-bugs.html
To do much more than follow the vendor's preferred disclosure process often amounts to demanding that *your* bug be given special attention and treatment. Which is a thing researchers sometimes do. Naturally it's hard to be objective about one's own finding.
Assessing and prioritizing bug reports is generally the job of the *vendor's* security team, *not* the researchers. There are exceptions. But to force special handling for your bug is simply to blindly take resources away from all the reports that will lead to the 487 other CVEs that month. And some of those might not be LPEs. They could be wormable remote network holes or virtual machine breakout bugs.
In this case, the kernel security team appears to have decided that the appropriate response was to let downstream read about it when the patch was committed to source control like everybody else. A CVE was publicly announced 11 days later, for a total of 30 days after being notified.
There are far worse systems.
Regardless, that process is theirs to manage. It's between the Linux kernel team and whoever they have made promises to.
I don't know about you, but I get my Linux for free. Nobody promised me anything.
* Data from stack .watch/product/linux/linux-kernel/, 14 month average
Wheeee! I've finally cleaned up the schematics and layout for the videothing TV transmitter board for release and updated the tinyvision library to work with it! Experience television like you never have before!
Go check it out! https://git.sr.ht/~slyka/videothing
RE: https://infosec.exchange/@wdormann/116495106231293342
Apparently it’s the fault of the researchers for reporting the bug to the Linux kernel security team, because they’re pumping out CVEs so fast that obviously no reasonable person could expect the combined efforts of commercial distros, cloud providers, and largest tech companies in the world to keep up with them.
Got a very silly #CopyFail container escape working.
Basically, if the container can see a file shared by the host, regardless of permissions, CopyFail can write to it on the host.
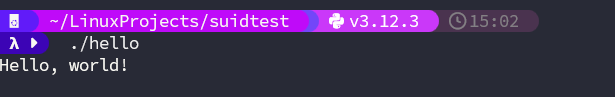
Okay I have one version of a container escape working. This relies on the fact that the page cache is shared between containers and host. There’s no isolation whatsoever. So if the container can see the file descriptor for a host file, copyfail works a treat. Let’s start with a simple C binary with nothing going on. It’s just a target. Now, we will mount that binary inside of an Alpine container in read only mode. Then after installing Python and a text editor, we modify the OG CopyFail...
trying a new thing, have 3D printed a QR code and put it on the front porch
QR code triggers a canary token
want to see if any of the delivery companies are using the drop off proof of delivery pics to train AI
Contrary to the implications of the (poor) vuln announcement and PoC, systems without suid binaries are NOT immune to https://copy.fail/
The vuln allows modifying anything in page cache, so an attacker can just modify the .text of any existing program running with privileges they shouldn't have.
RE: https://mastodon.social/@pid_eins/116459585811044061
Now I’ve seen everything 😂