Completed Part 3 of my personal #SocGholish series.
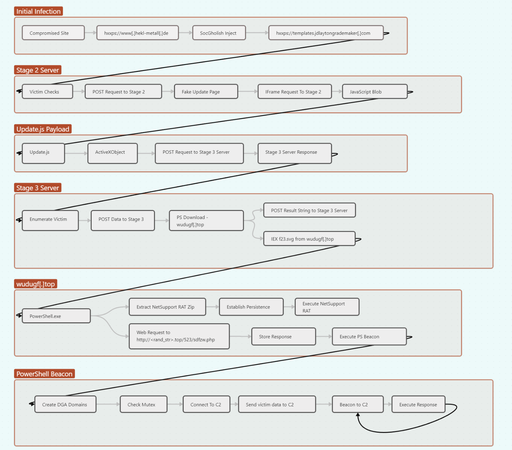
The article digs into the follow-up payloads delivered once the Update.js is executed on a victim machine.
Interestingly, I saw #NetSupport RAT and an unknown (to me) PowerShell C2 beacon be delivered together.
If anyone can shed more light on what the PowerShell beacon may be, it would be much appreciated! Seems to be inspired by #AsyncRAT, though.
Big thanks to @rmceoin for help along the way.
https://rerednawyerg.github.io/posts/malwareanalysis/socgholish_part3
SocGholish Series - Part 3 :: Reverse Engineering and Analysis — Reverse Engineering and Analysis
This is a continuation of my personal series on SocGholish (or FakeUpdates). At the conclusion of “SocGholish Series - Part 2”, I had obtained the primary, first stage JavaScript payload, titled Updates.js. In this writeup, I will execute the payload and observe the response(s) from the C2 server.