@kgndiue
- 6 Followers
- 64 Following
- 335 Posts
warming myself on this post like it's a space heater
RE: https://infosec.exchange/@adfichter/116379187239977403
Maybe we should send this to some decisionmakers in the EU?
RE: https://chaos.social/@fragdenstaat/116373611309376433
Das würde eigentlich reichen, um die Koalition platzen zu lassen.
I have read a statement
that “a whole civilization
will die tonight,
never to be brought back again,”
and as I read that statement
and as I reread that statement
I cannot shake the feeling
that the civilization
from which that statement comes
is one that is already dead.
that “a whole civilization
will die tonight,
never to be brought back again,”
and as I read that statement
and as I reread that statement
I cannot shake the feeling
that the civilization
from which that statement comes
is one that is already dead.
Es bleibt mir das große Rätsel, wie Menschen glauben können, Gesellschaften könnten sich nicht an etwas weniger Fleisch, andere Energieerzeugung, vielleicht eine Weile weniger Flüge oder Städte mit mehr Fahrradwegen anpassen, aber problemlos an eine 3 Grad heißere Erde.
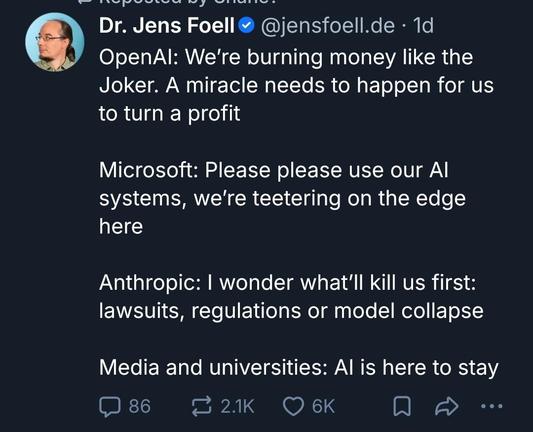
@davidgerard "They stole your code and your art, they built racism into their systems, they're eliminating your job or making it worse, they're enabling criminal fraud, they're trashing the environment, they're making computer hardware unaffordable, they're taking down your web site with their crawlers, and they’re about to crash the economy. Also, their technology is being used to drown out legitimate content with spam, push fascism, generate child porn, and target bombs at hospitals. So why won't you be civil to them and their fans? They just want to talk at you about exciting new uses for the technology, and bully you into accepting it by telling you it's inevitable and you'll be left behind if you don't use it. Your gatekeeping is a tragedy, we should be welcoming them to Mastodon, otherwise number won't go up."
I teach cybersecurity. And I genuinely don't know what to tell my students after this one. Federal reviewers spent years trying to get basic encryption documentation from Microsoft for its GCC High government cloud. They couldn't get it. One reviewer called the system a "pile of spaghetti pies," with data traveling from point A to point B the way you'd get from Chicago to New York: a bus to St. Louis, a ferry to Pittsburgh, and a flight to Newark. Each leg is a potential hijacking. They knew this. They said this out loud in writing. Then they approved it anyway in December 2024, because too many agencies were already using it. 🔐 That's not a security review. That's a hostage negotiation. Two things in this story should make every CISO and CIO uncomfortable:
🧩 Microsoft built its federal cloud on top of decades of legacy code that it apparently can't fully document itself
👮 "Digital escorts" often ex-military with minimal software engineering backgrounds are the firewall between Chinese engineers working on the system and classified U.S. networks 🤦🏻♂️
The scariest line in the whole ProPublica investigation isn't the "pile of shit" quote. It's this: FedRAMP determined that refusing authorization wasn't feasible because agencies were already using the product. Read that again. The security review process reached a conclusion based on sunk cost, not risk. Ex Post Facto Fallacy
If that logic holds, the compliance framework is just documentation theater. And right now, CISA is being hollowed out, so there are fewer people left to even run the theater.
https://arstechnica.com/information-technology/2026/03/federal-cyber-experts-called-microsofts-cloud-a-pile-of-shit-approved-it-anyway/
#Cybersecurity #Microsoft #FedRAMP #Leadership #RiskManagement #security #privacy #cloud #infosec
RE: https://bonn.social/@ulrichkelber/116357603860640008
Naja also welchen Wert hat es denn sich noch anzuschauen was beschlossen wird?
Ist ja nicht so, dass bei dem Fascho Scheiß den CDU und SPD momentan produzieren, Kritik helfen würde oder gar wahrgenommen wird.
“Oh no, people don’t like my bullshit here, in the open space I can set up any server I wish at all at any time, with little to no technical boundaries! quod erat demonstratum, it is _they_ who are wrong and I am being unfairly impinged! *pout*”
Go make your prompt-friendly server, Scott! It can host as many promptfans as you desire it to have! The rest of the network does not owe you followers or fawning https://social.coop/@scottjenson/116352800579635299
Scott Jenson (@[email protected])
As this conversation is spiraling a bit I want to make a few things clear: 1. I'd like Mastodon to be MORE inclusive and bring in more voices 2. Some people don't seem to want that 3. This is core problem to solve: How do we let more in, but not "pollute" your feed? 4. The solution is NOT "gatekeeping", revelling in the fact that AI journalists aren't welcome 5. This is the same reason we lost "Black Twitter" when it came over in 2022 Yes, a lot of you don't want AI posts in your feed (or pick any other topic) but the solution isn't to keep "AI People" from joining Mastodon, any more than it is keeping marginalized communities off of Mastodon.