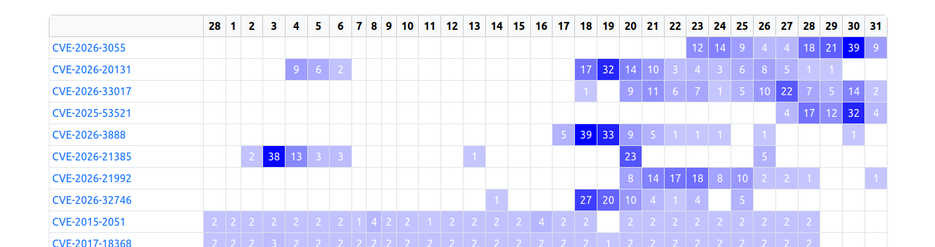
If someone comes to me today preaching about “post-quantum” security issues, I’ll remind them of the current state of security: the npm ecosystem gets abused daily, CI pipelines run left and right with full access to cloud services, so-called security devices like F5 and Ivanti are exposed (and compromised) to the internet, mailboxes get compromised just to change an IBAN in a PDF, and a simple phone call is still enough to get someone to hand over an MFA code.
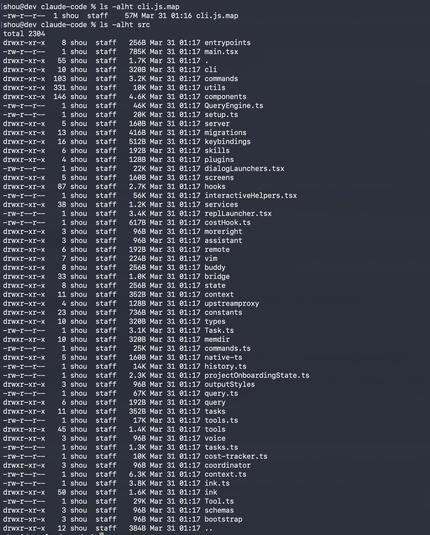
But yes, by all means, let’s focus on post-quantum threats while handing AI tools SSH access like it’s a feature, not a confession.
#cybersecurity #stateoftheworld