| GitHub | https://github.com/jamiemccarthy |
| Pronouns | He/him |
Jamie McCarthy
- 123 Followers
- 241 Following
- 568 Posts
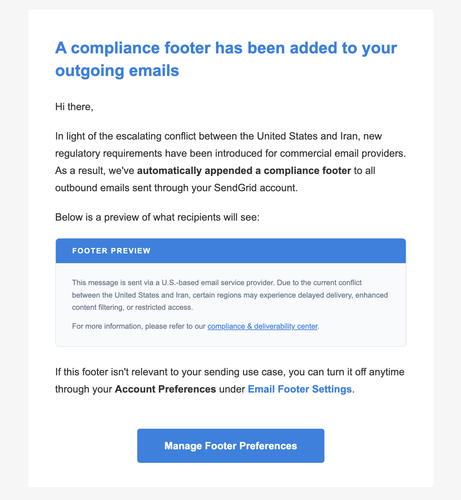
The bad guys have been crawling around Sendgrid's networks for over a year now, and they have news hounds writing their phishing text. Highly topical.
(Every link in here, even "unsubscribe," is a phish to, presumably, steal the credentials of the next customer)
The Sendgrid phishing network is getting political, telling its would-be victims: we're putting a pride banner on all your outgoing emails, click our phishing link to remove it.
This is a nine-figure ARR company that's had the bad guys phishing their way through its clients for the last ten months. Has anyone even noticed?
(This is not the CEO's name btw)
Holy shit, I think this is the most sophisticated hacked-Sendgrid phishing attempt yet. Someone apparently pwned a random server owned by selfcast[.]net and is sending Sendgrid email, aimed at Sendgrid admins, with links pointing to it.
selfcast[.]net appears to be a site for actors, but at first glance could plausibly be an alternate domain for an email-sending site. Nope!
The first link in the email looks valid; only the big tempting button is the phish hook
Lately, I've been using LLMs more for code investigation than for code generation. Here's Augment in VS Code spitting out a code flow diagram instantly instead of me jumping between files and building a mental model in my head to understand what's going on.
After a few months' pause, the phishing Sendgrid email fake-alerts have started back up this week. They still look pretty realistic! I almost clicked!
The headers show the phishing email as coming from Sendgrid's servers, because it actually is (this customer of theirs was hacked):
Received: from wrqvtcrk.outbound-mail.sendgrid.net (wrqvtcrk.outbound-mail.sendgrid.net. [149.[redacted]])
by mx.google.com with ESMTPS id 3f1490d57ef6-e75c0f0177esi1110886276.78.2025.05.06.03.09.59