If you have a Sendgrid (Twilio) account, be aware that for six weeks bad guys have been pwning Sendgrid accounts by spear-phishing Sendgrid admins via previously-compromised Sendgrid accounts.
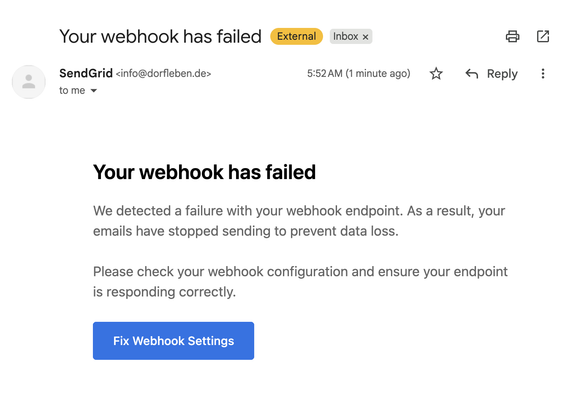
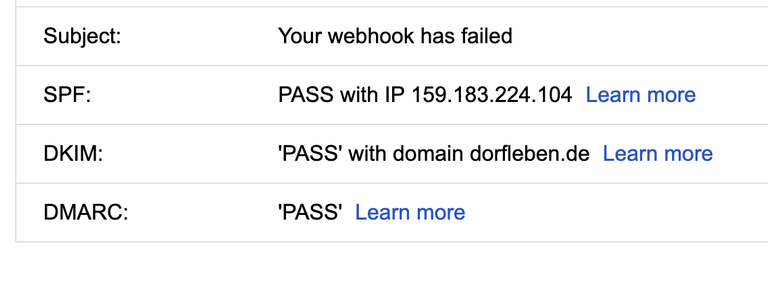
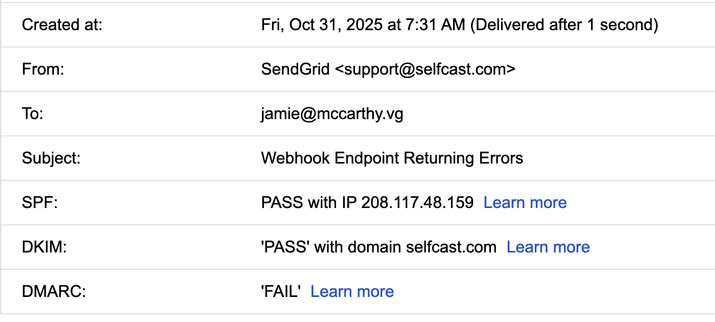
The emails come from Sendgrid's servers so they are unlikely to go into your spam folder. They pass SPF etc. because they are actual emails from Sendgrid, sent by a compromised customer.
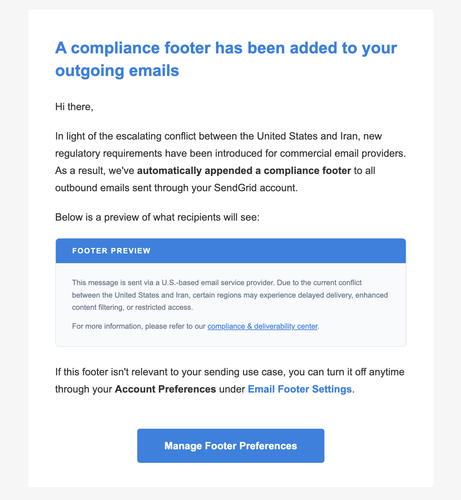
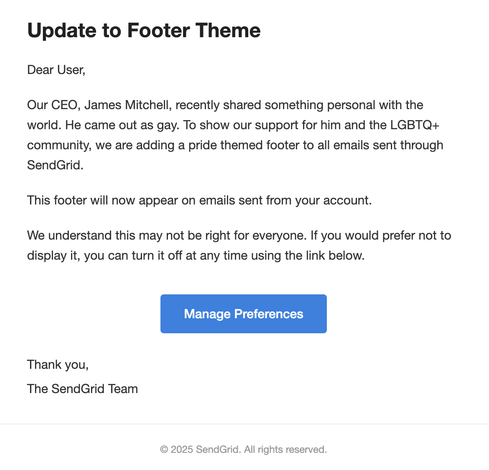
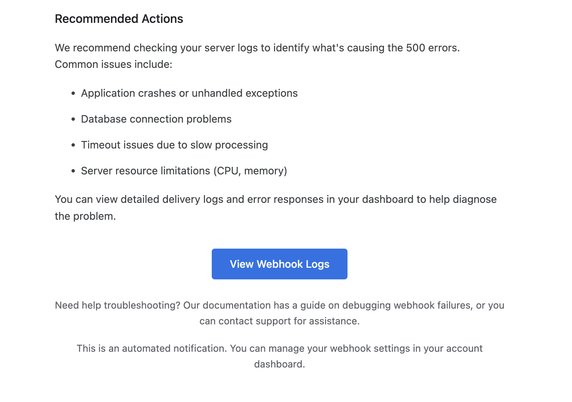
They look pretty realistic.