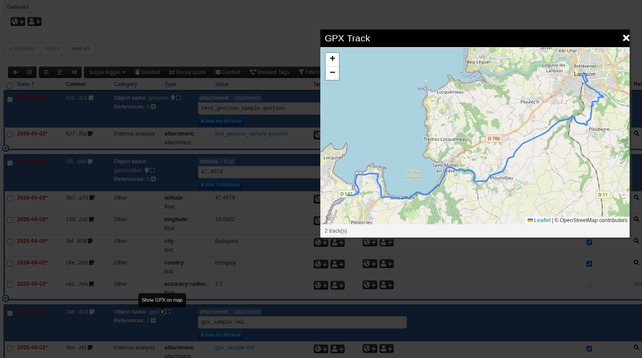
We are happy to announce the release of MISP v2.5.36, which includes new geolocation and map visualisation capabilities, the continued development of the Overmind UI, a new interactive CLI shell UI, important security fixes, and installer improvements.
Andras Iklody
- 523 Followers
- 197 Following
- 104 Posts
By the way, if you want to join us at hackathon.lu 14-15 April 2026 and work on some cool stuff, don’t hesitate to join us.
I have some free vouchers for the registration, ping me.
Oracle have laid off 30k employees today. They did it to personal email accounts at 6am 🫡 saying they needed the money to spend on GenAI instead. https://thenextweb.com/news/oracle-layoffs-march-2026
Oracle’s share price since they went GenAI nuts:
🪲 Bug Fix in pure-magic!
I just fixed a tricky offset computation bug in pure-magic, your pure Rust port of libmagic for safe file identification. So, make sure you are using the latest version available for your toolings.
🔎 Check it out
- Rust Crate: https://crates.io/crates/pure-magic
- CLI Tool (replaces file): cargo install wiza
- Python Bindings: https://pypi.org/project/pure-magic-rs/
- Repository: https://github.com/qjerome/magic-rs
RE: https://toad.social/@KimPerales/116296287470500816
Hope this isn't true, what guarantees are there for other EU-US collaborations that the funds won't be redirected?
https://infosec.exchange/@KimPerales@toad.social/116296287808070299
An authentication bypass in Ivanti Endpoint Manager before version 2024 SU5 allows a remote unauthenticated attacker to leak specific stored credential data.
#cybersecurity #ivanti #vulnerabilitymanagement #vulnerability
Thanks @reverseics for the infographics and Ivanti for the continuous source of discoveries.
@briankrebs just cancel the Olympics and the FIFA World Cup as the next step.
I will not travel to the US in 2026 just as sure as I would not recommend time travel to Germany 1936 to a jew.
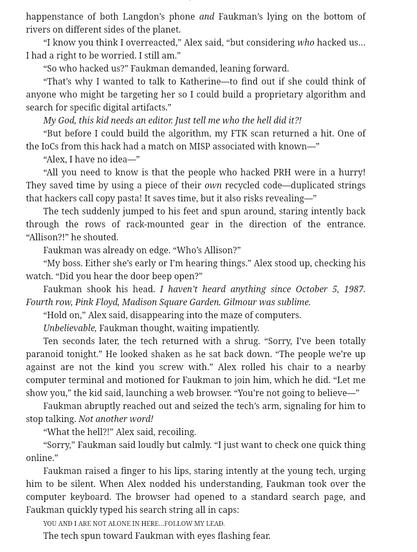
Someone asked me, “Have you read the latest Dan Brown?” There’s actually a mention of MISP in The Secret of Secrets. And yes, it fits surprisingly well within the story. Alex Conan (who assists Jonas Faukman in the investigation) mentions that he detected the activity using FTK, and that the indicators were later reused by the threat actor (having a hit on a MISP instance).
“But before I could build the algorithm, my FTK scan returned a hit. One of
the IoCs from this hack had a match on MISP associated with known—"
“Alex, I have no idea—"
“All you need to know is that the people who hacked PRH were in a hurry!
They saved time by using a piece of their own recycled code—duplicated strings
that hackers call copy pasta! It saves time, but it also risks revealing—"
French government always talks about technological sovereignty…
Why it matters to create and maintain open-source infrastructure for security monitoring including collection of forums and malicious communication channels.
This is a strong example (Google dark web report is discontinued) of the risks of relying solely on commercial vendors. If a capability does not align with their business interests or generate sufficient revenue, it can be discontinued at any time. Open-source infrastructure helps ensure continuity, transparency, and long-term access to critical monitoring capabilities that are essential for the security community.
If you want to run your own "darkweb" monitoring, we develop open source tooling supporting such monitoring
#darkweb #opensource #osint #cybersecurity
🔗 https://support.google.com/websearch/answer/16767242?hl=en&ref_topic=7028834&co=GENIE.Platform%3DiOS