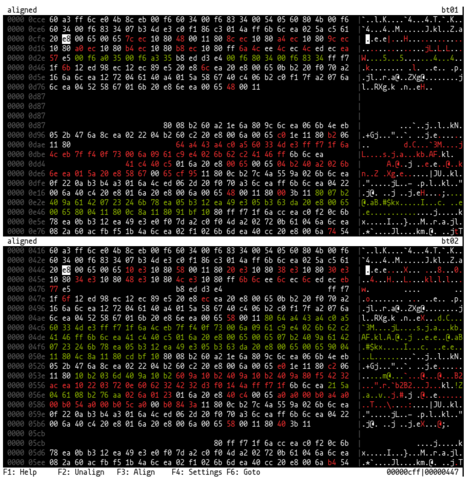
As many as 30,000 internet-facing Cisco routers and switches running IOS XE have been infected with implants after exploitation of CVE-2023-20198: https://vulncheck.com/blog/cisco-implants #infosec
Cisco's Talos has a blog here: https://blog.talosintelligence.com/active-exploitation-of-cisco-ios-xe-software/