Fredrik Dahlgren
- 39 Followers
- 114 Following
- 171 Posts
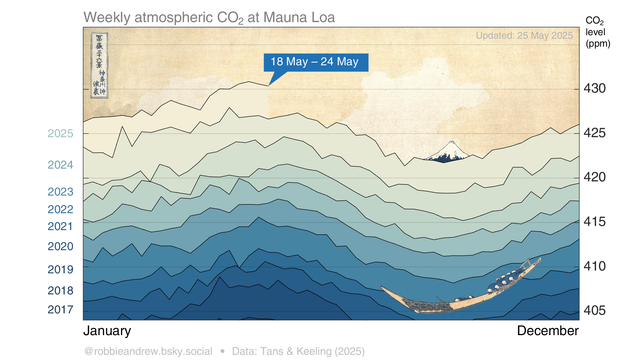
"The Great Wave" of carbon dioxide (CO₂) #ClimateChange #ScienceArt
Graphic produced by https://robbieandrew.github.io/
“Computers are useless. They can only give you answers.”
- Pablo Picasso
Case in point: there's no way to build a backdoor that only the "good guys" can use.
When the entire technical community says that the EU's ChatControl legislation + similar pose serious cybersecurity threats, we're not exaggerating for effect.
Computer Scientists Combine Two ‘Beautiful’ Proof Methods
Source : Quanta Magazine / Ben Brubaker
https://www.quantamagazine.org/computer-scientists-combine-two-beautiful-proof-methods-20241004/
#mathematics #maths #math
https://www.dn.se/sverige/sverige-staller-sig-bakom-chat-control/
https://pwner.gg/2024/10/03/llama-cpp-cves/
Pwning LLaMA.cpp RPC Server
Hello world, and Shana Tova :D I took the last few days to develop an RCE exploit by leveraging CVE-2024-42478(arb read) and CVE-2024-42479(arb write). Note: For a more detailed version of the exploit-dev process, see https://youtu.be/OJs1-zm0AqU The bugs The bugs are pretty documented in the GitHub advisory GHSA-5vm9-p64x-gqw9 and GHSA-wcr5-566p-9cwj. They are pretty trivial, but fun to exploit :D Achieving RCE To achieve RCE, i overwrote one of the callbacks of ggml_backend_buffer::iface: struct ggml_backend_buffer_i { const char * (*GGML_CALL get_name) (ggml_backend_buffer_t buffer); void (*GGML_CALL free_buffer)(ggml_backend_buffer_t buffer); void * (*GGML_CALL get_base) (ggml_backend_buffer_t buffer); void (*GGML_CALL init_tensor)(ggml_backend_buffer_t buffer, struct ggml_tensor * tensor); void (*GGML_CALL set_tensor) (ggml_backend_buffer_t buffer, struct ggml_tensor * tensor, const void * data, size_t offset, size_t size); void (*GGML_CALL get_tensor) (ggml_backend_buffer_t buffer, const struct ggml_tensor * tensor, void * data, size_t offset, size_t size); bool (*GGML_CALL cpy_tensor) (ggml_backend_buffer_t buffer, const struct ggml_tensor * src, struct ggml_tensor * dst); // dst is in the buffer, src may be in any buffer void (*GGML_CALL clear) (ggml_backend_buffer_t buffer, uint8_t value); void (*GGML_CALL reset) (ggml_backend_buffer_t buffer); // reset any internal state due to tensor initialization, such as tensor extras }; struct ggml_backend_buffer { struct ggml_backend_buffer_i iface; ggml_backend_buffer_type_t buft; ggml_backend_buffer_context_t context; size_t size; enum ggml_backend_buffer_usage usage; }; This is triggered every time the client sends a GET_TENSOR command: b3560/ggml/src/ggml-backend.c#L246: GGML_CALL void ggml_backend_tensor_get(const struct ggml_tensor * tensor, void * data, size_t offset, size_t size) { ggml_backend_buffer_t buf = tensor->view_src ? tensor->view_src->buffer : tensor->buffer; GGML_ASSERT(buf != NULL &&
🇬🇧Thanks to tireless digital freedom fighters in science, NGOs and politics, #ChatControl had to be removed from today's agenda again because there was no qualified majority in sight! 🥂🥳 https://netzpolitik.org/2024/eu-rat-chatkontrolle-von-der-tagesordnung-genommen/
But no sign of a rethink: it remains on the agenda for the meeting of home affairs ministers on 10 October. https://www.parlament.gv.at/dokument/XXVII/EU/197487/imfname_11411526.pdf
Our next goal: extend the blocking minority to a majority for a fundamental rewriting of this bill!
EU-Rat: Chatkontrolle von der Tagesordnung genommen
Die Mitgliedstaaten der EU sind sich weiterhin nicht einig über die Chatkontrolle. Eine Sperrminorität im Rat hat zum wiederholten Male dazu geführt, dass das Thema von der Tagesordnung genommen wurde. Derweil melden sich noch mehr Kritiker der Chatkontrolle zu Wort.