What have I done ??!
@drm
- 20 Followers
- 59 Following
- 109 Posts
🆕 New blog post!
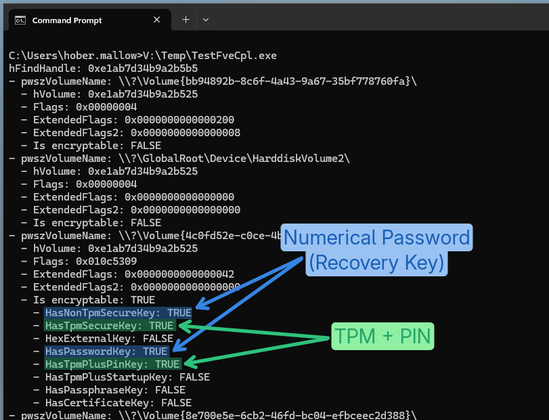
"BitLocker's Little Secrets: The Undocumented FVE API"
A small Windows RE adventure to figure out how to get the status and configuration of a BitLocker protected drive programmatically and without admin privileges.
Now also implemented in PrivescCheck! 🔥
👉 https://itm4n.github.io/bitlocker-little-secrets-the-undocumented-fve-api/
A private Burp Suite Collaborator instance is an essential for pentesting sensitive environments, but managing TLS for it can be a pain. Today we release a Certbot plugin that automates Let’s Encrypt wildcard certificate renewals for private instances.
https://github.com/AlmondOffSec/certbot-plugin-burpcollaborator
Are one-way trusts really one way? @drm sums up how the TDO password lets you turn a one-way AD forest trust into bidirectional access, and releases a new tool to remotely extract these secrets.
https://offsec.almond.consulting/trust-no-one_are-one-way-trusts-really-one-way.html
I was bored to type the same commands each time I started a new internal pentest. So here comes KingCastle. This script does not perform any attacks, consider it as a cheat sheet, to quickly see low hanging fruits.
https://github.com/ThePirateWhoSmellsOfSunflowers/KingCastle
Team member @sigabrt was able to bypass Apache FOP Postscript escaping to reach GhostScript engine.
https://offsec.almond.consulting/bypassing-apache-fop-escaping-to-reach-ghostscript.html
Changelog: https://www.wapt.fr/fr/doc/wapt-changelog.html#wapt-2-6-1-17705-2026-02-04
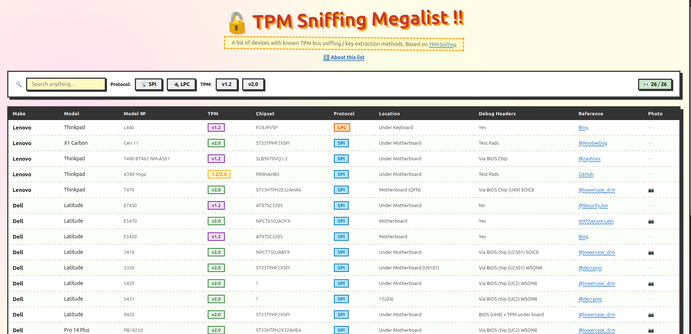
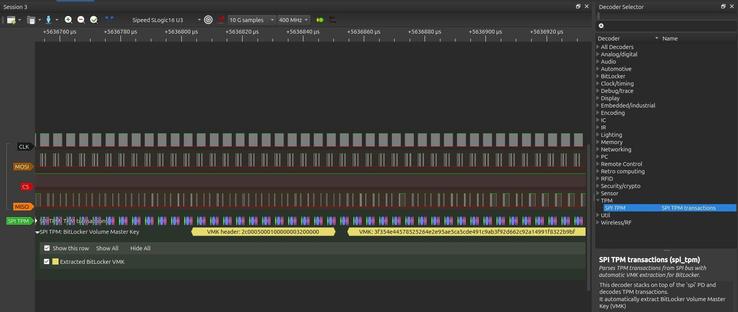
TPM sniffing is cheaper than ever
https://www.cnx-software.com/2025/11/12/69-sipeed-slogic16u3-low-cost-logic-analyzer-supports-3-2-gbps-bandwidth-150-protocols/