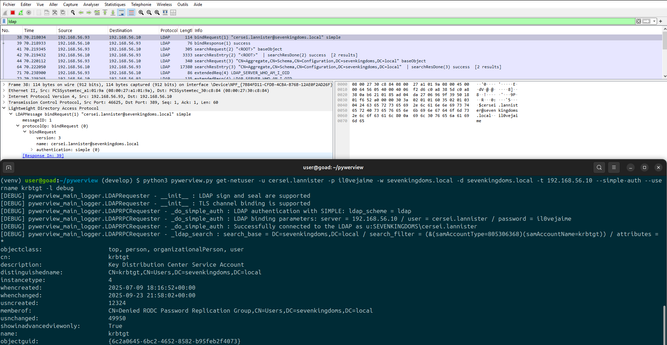
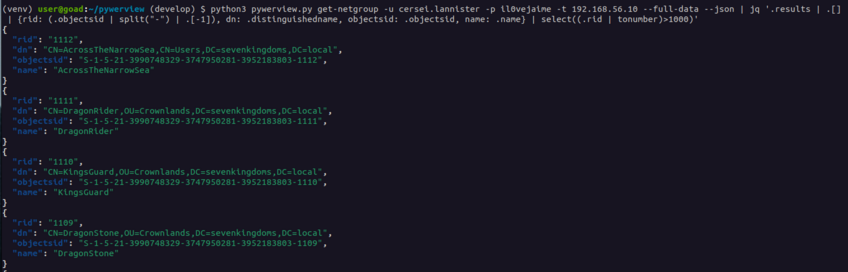
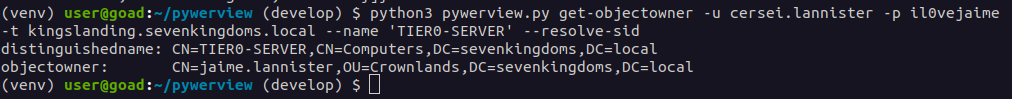
Recently, a colleague encountered a strange situation: an undetermined security product was killing LDAP connections performed by ldap3 (NTLM). A simple bypass was to force SIMPLE authentication (pun intended). I've implemented it in #pywerview.
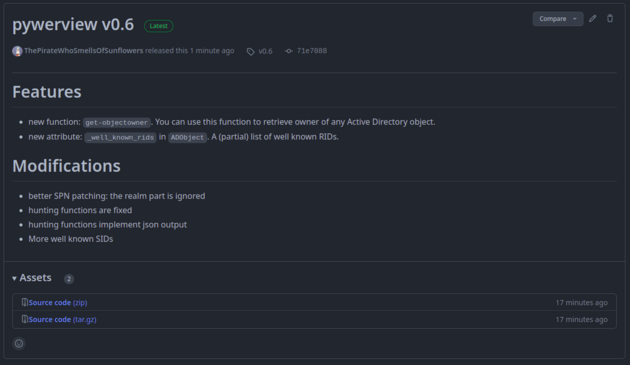
https://github.com/the-useless-one/pywerview/tree/develop
🌻